Bellingcat has geolocated and verified two new videos showing the deadly strikes that hit an Iranian Revolutionary Guard Corps (IRGC) compound as well as an adjacent school in the city of Minab in late February. The new videos were released by Iran’s Ministry of Foreign Affairs and show multiple missiles hitting the complex. One of […]
The post Two Waves of Bombing: New Videos Reveal Further Details About Iran School Strike appeared first on bellingcat.
The US appears to have deployed the Gator Scatterable Mine system over Kafari, a village near Shiraz, in southern Iran overnight. Several people were killed according to Iranian media. Three experts told Bellingcat the munitions appeared to be air-delivered US-made Gator anti-tank mines. The US is the only participant in the Iran war known to […]
The post Evidence Points to US Scattering Mines over Iranian Village appeared first on bellingcat.
Munition remnants pictured at the site of a strike that killed at least 17 people in the town of Tiné, Chad, last week appear to match a weapon previously used by Sudan’s Rapid Support Forces (RSF) in the war with Sudanese government forces – despite RSF denials of involvement in the incident. Photographs showed what […]
The post Munition Remnants Pictured at Site of Deadly Chad Strike Match Weapon Previously Used by Sudan’s RSF appeared first on bellingcat.
A Bellingcat investigation has identified nine Facebook groups with a combined membership of more than 70,000 people, in which coded language has helped illegal wildlife dealers evade bans on the platform for years. Facebook says it prohibits any form of animal trading on its platform. Investigating the operators behind all nine groups, Bellingcat identified six […]
The post How Wildlife Traffickers Are Using Coded Language to Sell Protected Animals On Facebook appeared first on bellingcat.
This investigation is part of a collaboration between Bellingcat, Evident Media and CalMatters. You can watch Evident’s investigative video here, and read CalMatters’ report here. In early January 2025, a gardener named Ernesto Campos was pulled over by Border Patrol agents in the city of Bakersfield, California. The agents were a long way from home: Bakersfield […]
The post Agents of Chaos: Unpacking the Actions of Border Patrol Agents Across the US appeared first on bellingcat.
This article is the result of a collaboration with The Sunday Times. You can find their corresponding piece here. Bellingcat and The Sunday Times last week published photographs showing ex-UFC fighter Mounir “The Sniper” Lazzez with wanted cartel leaders Christy and Daniel Kinahan. The images, captured during the 971 Fighting Championship in Dubai last June, […]
The post Ex-UFC Fighter and Kinahan ‘Friend’ Mounir Lazzez Linked to Iran Sanctions appeared first on bellingcat.
The Netherlands’ largest newspaper, De Telegraaf, recently published an interview with a woman claiming to organise her own evacuation flights from Dubai, selling seats at €1,600 (US$ 1850) each. Four days later, her photo was removed from the article, though the interview remained. Bellingcat has found that the original image not only includes artefacts commonly […]
The post AI Used to Promote Non-Existent Evacuation Flights From the Middle East appeared first on bellingcat.
To stay up to date on our latest investigations, join Bellingcat’s WhatsApp channel here. Bellingcat has geolocated footage of multiple Tomahawk cruise missiles travelling through Iraqi airspace towards Iran, either in violation of its airspace or with Iraq’s consent. Bellingcat identified at least 20 individual cruise missiles and geolocated them over Iraqi Kurdistan including alongside Mount […]
The post Tracing Tomahawks: US Missiles Bound for Iran Spotted Over Iraq appeared first on bellingcat.
New video footage shows a US Tomahawk missile hitting an Islamic Revolutionary Guard Corps (IRGC) facility in Minab, Iran, on Feb 28, showing for the first time that the US struck the area. The footage, released by Mehr News and geolocated by Bellingcat, also shows smoke already rising from the vicinity of the girls’ school […]
The post Video Shows US Tomahawk Missile Strike Next to Girls’ School in Iran appeared first on bellingcat.
This article is the result of a collaboration with The Sunday Times. You can find their corresponding piece here. Kinahan cartel leaders Daniel and Christy Kinahan have been photographed in Dubai, marking the most recent sighting of the wanted crime bosses since the US government put multi-million dollar bounties on their heads. The footage was […]
The post New Footage Shows Wanted Kinahan Cartel Kingpins Post-Sanctions appeared first on bellingcat.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of February.
At the start of the month, we spent a delightful couple of days deep in the wintry and rainy Spanish countryside, gathered in a medieval monastery with the Ink & Switch team for the 10 years anniversary of the studio. We also met up with Javier and Marcelino who gave us coffee and a book on celestial navigation, we will savor a cup while studying the sky.
We asked folks on the fediverse for their favourite rabbits from Rek's recent series, and picked out the four most popular and made stickers. We received them just yesterday and they look amazing! Thanks to everyone who already asked for a sheet! We pack the letters by hand, and Dev makes a spirograph on the back of each one encoding the date in gear radius and ratio.
We've hit some annoying issues with Arch, where mainstay programs sudden change their behavior or gets abandoned like volumeicon. Being unable to control the master volume without opening a full GUI application is a pain. Devine to the rescue! An hour's work and Pavol was born! In that same vein, while working on the new version of Donsol, we realized we'd need to design fonts larger than 16 px high, something that Turye was incapable of doing, until now.
On March 6th, we'll be giving a talk at the University Of Victoria, to talk about how our 10 years of living on the water has influenced our design and development work. The event is sold out at this point, but if you signed up see you there! Oquonie for Playdate will be on Playdate's upcoming Catalog Anniversary Sale running from March 5th to March 19th.
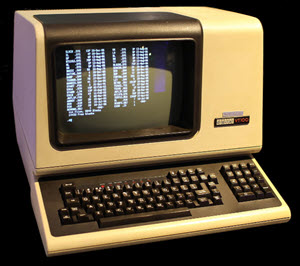
Devine has been puzzling over an extremely odd programming language idea and is looking for some pointers, prior art, ideas, so if ferns, rewriting, confluence, linear logic, tensor and multisets mean anything to you and interests you, get in touch. Lastly, we'll leave you with this image of Polycat working on a 2009 EeePC under HaikuOS, courtesy of Tbsp!
Book Club: We finally finished reading Middlemarch by George Eliot, a very good read, we will miss it. We are also reading Red Plenty by Francis Spufford and This Is How You Lose the Time War by Amal El-Mohtar and Max Gladstone. We also watched great movies like The Battle of Algiers(1966) and Z(1969).
Hey everyone!
This is the list of all the changes we've done to our projects during the month of January.
This is likely very obvious to most people, but recently it dawned on us that clothes are, in a certain way, open-source. We can go to a thrift store, buy a shirt, rip out the seams, study it, lay all of the pieces down over new fabric, trace the patterns, cut them out, and sew it all back together to produce a copy of that same shirt. We've been wanting to learn how to make our own clothes but didn't know where to begin, until this month. Our first project was to reproduce our hats, after the store we bought them at stopped stocking them. We bought black cotton canvas at a local fabric store, took our old hats apart and re-built them(See Rek's hat, and Dev's hat). Later, Devine did the same for our old messenger backpack.
Goblin Week, an event in which people draw goblins for 7 days, occurs on the last full week of January. Devine's entries were inspired by a passage in Samuel Butler's Erewhon, and Rek drew some spunky cartoony goblins.
Inspired by Prahou's Subversive.pics, we put together image feeds for our personal websites.
Note that we are still uploading photos to Days, our studio's image feed.
We are making progress on the Playdate version of Donsol, and the polished manuscript for the Victoria to Sitka Logbook. We do not yet know when either will be finished so let us end this updated with one last small thing: a video by VacuumBeef of Snake Game in Orca.
Book Club: This month we have reached book 8 of Middlemarch by George Eliot, the very last one. We are also reading Mémoires d'Hadrien by Marguerite Yourcenar, and Amusing Ourselves to Death: Public Discourse in the Age of Show Business by Neil Postman.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of December.
It's that time of the year when we look back to our many bird encounters, account for what was damaged and mended, reminisce about moments immortalized in our paper calendars, and think of the many projects that have yet to leave the pages of our notebooks. We'd like to thank everyone who wrote to us, especially those who have tirelessly corrected errors in our writing and code, and we want to do a shoutout to the members of Merveilles, as well as artists, thinkers and tinkerers everywhere for inspiring us.
We kicked off January with the release of the 1-bit version of Oquonie for Playdate. It would be the first time, since the iOS version, that the game has a soundtrack. Devine also improved the html5 Uxn emulator to make all of our games and tools playable in the browser. Uxn's list of utilities has grown, with additions like a spreadsheet editor, a font editor, a theme editor and a desktop calendar.
rabbit Waves has grown by five new topics this year, and we have since assimilated this knowledge into daily life. On many summer evenings, we were out on deck scanning the skies for the Big Dipper, the Little Dipper, and Cassiopeia. Polaris sits 1 degree away from the celestial north pole, neither of us had ever truly appreciated this incredible fact until now and we can't think of any piece of knowledge that has so deeply touched us. Learning about field care also had a lasting effect on us, since then we carry a First-Aid kit whenever we go out on a long hike.
In early May, we set sail for Texada Island for a haul-out. This will be as far north as we would go this year, because we had to sail right back down again to meet up with friends on Blakely Island. After the event, we had yet another place to be, we pointed our bow west and sailed out of the Juan de Fuca Strait. Pino arrived in Ucluelet just in time to attend a friend's presentation to the city council about building a new boatyard. The rest of our summer schedule was not as rigid, we spent time amongst hummingbirds, met beautiful cetaceans, solar-cooked breads and played dominos aboard wooden boats.
In December, our usual afternoon walks were often spoiled by heavy rainfall. The prolonged absence of sunlight, the constant downpours, turned Pino's topsides green. Like in Ray Bradbury's short story All Summer in a Day, our world was all rainstorms. We were too glad when the clouds parted on the winter solstice. Every year, December ends with us folding big prisms out of modular orgami techniques, especially sonobes. This year's masterpiece was a stunning triakis icosahedron made of colorful construction paper. We also played through The Neverhood drinking hot spiced apple juice. We've since been exploring other Scummvm games.
In the recent onslaught of slop, we are continually impressed and inspired by artists and developers who fight back against the machine learning spear that is pointed toward them. Choose human agency, sabotage agents! See you in 2026!
Our favorite series this year was Scavengers Reign and Common Side Effects, and ours favorite films were Sinners and Nosferatu.
Book Club: This month we are still reading Middlemarch by George Eliot, but Devine also finished Blindness by José Saramago and Rek started paging through Make, Sew and Mend by Bernadette Banner.
Devine's favorite read of the year was Donna Tartt's The Secret History, and Rek enjoyed and cried over Girl's Last Tour by Tsukumizu.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of November.
This month, we celebrate Hundred Rabbit's 10 year anniversary and remember with great fondness how, in November 2015, we sat together at a coffee shop in Montreal, puzzling over how we would start a new life on the water. Here's hoping for 10 more years of learning and documenting experiments around low-tech and resilience!
We finally stashed our summer sailing gear, we compressed everything into vacuum bags drawing out as much air as we could to discourage mold. We're entering the month of December in Victoria, and we are beginning to feel the increasing dampness of winter in our clothes, we also see it as the condensation gathers on Pino's windows.
Devine spent the last few days in Austria for the Ultramateria Festival talking with local artists and activists about the design philosophy of Hundred Rabbits. Devine also gave an Orca workshop, played some techno in a gorgeous venue, made a brief appearance on Austrian television and Fireside Fedi.
Rek spent time troubleshooting a raw water leak in Calcifer II, gaining in-depth knowledge of yet another part of the engine. What was learned was documented in the ever-growing engine care portal under raw water pump. Rek has also been working on the upcoming Playdate version of Donsol!
Book Club: This month we are still reading Madame Bovary: Provincial Manners by Gustave Flaubert.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of October.
We sailed Pino back to Victoria before heading east for AMP Festival 2025. The venue was packed! The Aliceffekt show(YouTube) started with a bit of radio taiso, to make sure everyone had a chance to limber up, it was pretty funny.
As the trees were shedding the last of their leaves, members of the Merveilles community composed a spooky mixtape(download), and we folded paper to craft ourselves some homemade Halloween masks. Like every year, we carved a pumpkin. This year's design was inspired by the Hollow creature from the amazing animated sci-fi series Scavengers Reign.
We spent the rest of the month with family, seeing friends and reviewing microgrant applications for Rhizome.
We have re-opened the store for sticker sales, but at the moment we cannot ship them to the US due to the suspension of the de minimis exemption. We hope to resume shipments as soon as we can figure out how to comply with the new shipping rules. The sale of our physical books to the US is unaffected. We'll end this update with the mention that Oquonie is part of the Playdate Catalogue fall sale lasting until Nov 13, 2025. Thank you to everyone who continue to explore our strange little world.
Book Club: This month we are reading The Outsiders by Susan E. Hinton, and Madame Bovary: Provincial Manners by Gustave Flaubert.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of September.
As promised, we released a revised transcription of Devine's talk Permacomputing 101 for Critical Signals 2025! We have moved our website to a Canadian TDL(100r.ca), so be sure to update your bookmarks! We will keep the .co version of our website online for redundancy.
Rek finished revising the upcoming version of the Victoria to Sitka logbook and passed the text over to Devine for proof-reading. The finished publication will feature 104 drawings, 19 recipes, and 18 new sections on a variety of topics. We hope to release the digital version early next year, and the printed version a bit later.
Our friend Erik(d6) designed a bespoke chat server so that the Uxn community could meet up through an interface designed specifically to interface nicely with tiny clients so we hacked together a little rom for it. Get in touch if you'd like to hang out on there!
Devine is performing in Montreal on October 11th, as Aliceffekt, at the AMP Festival 2025. They've also released a new album this month, called Ver'Iystl(Bandcamp), adding further dimension to the many places populating the Neauismetica. Let us know if you're planning to come!
Book Club: This month we are reading The Glass Bead Game by Hermann Hesse, and we are continuing to read Middlemarch by George Eliot.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of August.
In preparation for a programming class that's coming up, we've implemented a graphical tiny-BASIC runtime called Sunflower BASIC. It contains the essential blocks of a BASIC language interpreter with enough features to communicate elementary programming concepts and how each one is implemented. We've also released the Permacomputing 101 talk given at Critical Signals 2025 which covered a few interesting aspect of digital preservation and some tactics to craft software in a way that may last.
Choosing to remain in the Southern Gulf islands in August this year has permitted us to pick blackberries, plums and apples. We have incorporated the fruit into cakes, or just squished whole berries over morning toast. We processed some of the apples into jam, and are currently delighting in eating through the rest. We've also been experimenting with the solar cooker, preparing some cinnamon buns in it for the first time! See our cameo in our friend Peter's latest video.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of July.
This month we sailed into the Juan de Fuca Strait, escorted by pods of orcas and a lone young humpback whale. The last time we had been here was in July 2020, on our way back from Japan. After weathering gale force winds at anchor in Becher Bay, we stopped in Port San Juan. The beaches there are covered in old growth driftwood, carried there by winter storms. Some trees are so large and have been there so long that people have installed swings on them. The way to Barkley Sound was bleak, we spent 10 hours of it in a fog bank, only to emerge near Cape Beale to a bright sun over jade-colored waters. We pulled into Ucluelet the next day, just in time to meet up with our friend Avi to view the building site for their upcoming boatyard project.
We spent a few days anchored in Barkley Sound, in an anchorage with the biggest population of hummingbirds we'd ever seen. The hummingbird visits were constant, with 3-4 buzzing around us at all times. During our stay there we completed our game entry for Catjam named Polycat. The game is very hard, but also very short. Watch a video of Devine playing the game.
In the second half of July, Pino sailed back to the Southern Gulf islands and stayed anchored alongside a friend, messing with their laser engraver, hiking, picking blackberries, and working on projects. Instead of hummingbirds, in Fulford, we had kingfishers, they really liked sitting on the wind vane's arrow on top of the mast. See this amazing drone footage shot by our friends aboard MV Poem.
Devine has been invited to talk about permacomputing at Critical Signals on August 12th. They will try to introduce some of the ideas that they find most interesting via practical examples. Save the date!
Book Club: This month we are reading Ancillary Justice by Ann Leckie.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of June.
For a few days, Pino became a land creature, living on stilts, while we scrubbed and re-painted the lower part of the hull. Our propeller had a bit of a wobble, which we hope is now corrected. We also battled with the old wheel quadrant and were finally able to remove it, at least a part of it. Boaters have frequently helped us while we were in boatyards, and we are finally able to pay it forward. We offered both advice to those who asked and lent tools to folks that needed them. It felt nice. Teapot's new bottom has seen water for the first time, the new gelcoat will allow us to take it around into bays for many more years to come.
We spent many June days working on both Turnip Complete(Uxn book) and the enhanced version of the Victoria to Sitka Logbook, with frequent breaks to enjoy the beautiful places we found ourselves in.
The beginning of our sailing season has been very blustery, allowing for some good sailing, but also often forcing us to wait at anchor for clement weather. Later, we sailed through the San Juan Islands to meet up with some Merveillans on Blakely Island. We are very grateful to be part of a community of such kind, curious, and generous people. The image that was drawn for this month's update represents cooperation between members of Merveilles.
Book Club: This month we are reading Ill Met By Moonlight by Sarah A. Hoyt, Silmarillion by J.R.R Tolkien and Girl's Last Tour by Tsukumizu.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of May.
Oquonie was released on the Playdate Catalog this month! We'd like to thank everyone who sent us photos of their progress in the game, it has been nice to follow along. The game is kind of our first official release on a modern handheld platform, and we're happy to see that Uxn roms run well on it! It might be one of the first original Playdate games implemented that way?
In other news, Devine started working on a book, the working title is "Turnip Complete". The goal is to write a complete and stand-alone implementation guide for the Uxn virtual machine and devices, along with some example programs and thoughts about playful computery things. We might have something to show for it come autumn, maybe.
We've left Victoria for the summer, and are falling back into the groove of waking up at dusk to catch the tide. We have a quick haul out lined up, and afterward we'll be sailing around the Gulf Islands until the fall. We have lots of projects to finish up these next couple of months and can't wait to share them with you.
We share photos of life aboard throughout the month on our little photo site, if you're curious to see what the daily life aboard Pino is like.
Book Club: This month we are reading Artemis by Andy Weir, Gardening Without Work: For the Aging, the Busy and the Indolent by Ruth Stout and A History of Thinking on Paper by Roland Allen.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of April.
The weather is getting warmer, which is perfect for airing out Pino's lockers, and drying off moldy clothes and tools. Anything stored in the v-berth lockers, below the waterline, suffer from extreme wetness. It is a very, very annoying fact of boat life, but there is really no way to bring good air flow in those spaces. We scrubbed the lockers clean, parted with items we no longer needed, and sent two laptops to the recycler.
In last month's update, we mentioned Flickjam, a game jam based on Increpare's Flickgame. We received a total of 27 entries! They're really fun, and all playable in the browser. Devine's jam entry is about a very adorable rabbit learning to play the word "rabbit" on a xylophone in Solresol.
Devine spent some time off the computer, skating and folding paper. The paper computer pages have been updated to cover some new ways in which computer emulators can be operated on paper. While on that subject, we highly recommend Tadashi Tokieda's excellent talk named A world from a sheet of paper.
Another item on Devine's list was to gradually phase out Uxnasm.c in favor of the self-hosted assembler. We're not 100% pleased yet, but it is getting closer to retirement.
Starting on May 20th 2025(1000 PST/PDT) the Playdate Catalogue will include Oquonie. The game is also available on our itch.io store.
The video for Devine's November 2024 talk A Shining Place Built Upon The Sand is now on YouTube.
Book Club: This month we are reading Banvard's Folly by Paul Collins, Einstein's Dreams by Alan Lightman, and we are still making progress on the The Goldfinch by Donna Tartt.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of March.
In the above illustration, little Ninj is going through a first-aid kit, looking through our supplies to see what needs to be topped off and what is out-of-date. Rek drew a list of suggestions on what to include in both a first-aid and a medical kit for the Rabbit Waves project, we plan to add more items soon(thanks to everyone on Mastodon who suggested additions! It'll be in the April update).
We will spend the first few days of April participating in Flickjam, making small games in the style of Flickgame, a tool originally made by Increpare, in which the world is navigated by clicking on pixels of different colors to head in different directions. Devine ported Flickgame to Varvara, and wrote a compiler for flick games to uxn roms.
This past month, Rek finished transcribing the entire 15 weeks of the Victoria to Sitka logbook! We have plans to turn it into a book, in the style of Busy Doing Nothing, with tons of extra content and illustrations.
March was a very good month for silly calendar doodles. Our paper calendar is always in view, it documents important events like releases, appointments, as well as food, memes, and other noteworthy things that happened on each day.
Book Club: This month we are still reading The Goldfinch by Donna Tartt(it's a long book).
Hey everyone!
This is the list of all the changes we've done to our projects during the month of February.
On February 14th, we celebrated our 9th year living aboard our beloved Pino. Read a short text by Devine, which expands on what it means to truly be a generalist.
Despite the weather being less-than-ideal, we were able to install our replacement solar panels, and revisit our notes on solar installations.
Devine completed Nebu, a spritesheet editor as well as a desktop calendar, alongside many other little desktop utilities. Nebu is just over 8.3 kB, a bit less than a blank excel file.
In times of increasing climate and political instability, it is a good time to get together with your community and make plans for emergencies. Consider reading Tokyo Bosai about disaster preparedness, this elaborate document deals with disasters that occur specifically in Japan, but many of the recommendations are useful regardless. We released a new page on rabbit waves with suggestions on what to pack in an Emergency Bag. Remember, every emergency bag is different, and what is essential varies per person.
We also put together a print-it-yourself zine, which combines useful information about Morse Code and Signal Flags. If you have printed the zine and don't know how to fold it, see Rek's illustrated instructions. Speaking of signal flags, we printed stickers of Rek's ICS flag drawings.
The nice weather finally arrived this week and we were able to redo Teapot's gelcoat. This was our first time working with gelcoat, our friends Rik & Kay, who lent us their workspace, were very patient and generous teachers. We will continue the project later when the gelcoat has cured.
Book Club: This month we are reading The Goldfinch by Donna Tartt.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of January.
Devine spent time improving the html5 Uxn emulator, and thanks to their hard work it is now possible to play Niju, Donsol, and Oquonie directly in the browser on itch.io, the same goes for projects like Noodle and Tote.
It's been a long time coming, but Oquonie is now playable on Playdate. Rek spent the last week converting the 2-bit assets for Oquonie to 1-bit, because some of the characters and tiles were too difficult to read, now all of the assets work perfectly on monochromatic screens. As an amazing plus, Devine got the music and sounds working perfectly, just like in the original iOS version.
From January 19-25th, we both participated in Goblin Week, an event in which you make goblins every day for a week(whatever that means to you). See the goblin series made by Rek(viewable here in higher rez also) and the one made by Devine(Mastodon).
Pino has earned two new replacement solar panels this month! We have not installed them yet, it is still too cold outside in Victoria (we are expecting snow this week).
We share photos often in our monthly updates, and so Devine spent time building our very own custom photo feed named Days. It is possible to follow the feed with RSS.
Book Club: This month we are reading How do You Live? by Genzaburo Yoshino and Middlemarch by George Eliot.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of December.
Before diving into the ins and outs of the past year, we'd like to begin by sending our very warmest thanks to everyone who generously hosted us, drove us to the hardware store, invited us out for fries to cheer us up, fixed typos in the books, improved the documentation, lent us power-tools, donated to the studio, spent hours to show us how to fix broken things and corrected us when we were wrong.
During the first few weeks of the year, we were busy with planning our upcoming sail north to Alaska, during which a DDoS attack took down many of our repositories and precipitated our decentralizing of the project source files. Mirroring our projects across multiple forges and diversifying the means in which they were available became necessary.
In preparation for the heavy weather up north, we strengthened the chainplates and replaced a few experienced halyards. In fact, our most vivid memories of the early spring was of the blisters we made splicing dyneema. We've also built ourselves a gimballed stove with space for an open pantry allowing us to store more fresh vegetables by doing away with the oven.
Our summer was spent exploring the Northern Canada and Alaskan coastline to test the recent boat projects, a sort of shakedown if you will, in preparation for plans we may divulge in a future update. During our transit, we began writing down notes on various forms of analog communication which have now mostly fallen into obscurity. These notes later became an integral part of the Rabbit Waves project, created with the hope of sparking an interest in these valuable but vanishing skillsets.
Through it all, we continued improving the Uxn ecosystem documentation and toolchain, which has played a central role in our work now for four years! We've also explored other enticing avenues where small robust virtual machines could be used for knowledge preservation, namely Conway's Fractran, which all came together into the Shining Sand talk given at the the year's end.
We're looking cautiously forward to the challenges that awaits us all in 2025. Approaching these adversarial forces with collective tactical preparedness and clarity is more important than ever, and we shall all rise to the occasion!
We had a lot of really good wildlife moments this year, and so the last drawing of 2024 is of a half-mooning seal.
Book Club: This month we are reading The Secret History by Donna Tartt. Our favorite book this year was West with the Night by Beryl Markham, see all of the other books we read in 2024.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of November.
Our website has a new look! The illustrated algae-eared rabbit nav helped solve the problem of navigating on mobile. We added a lot of information to this wiki over the years, creating separate portals for its evergrowing content was inevitable, we hope you like the re-design. Some of the content has shifted, and we've simplified many of the pages.
A couple of folks on Merveilles got together recently and made a Diablo Tribute tape. A limited run of physical cassettes are currently in production, but in the meantime the tribute album is available to download on Bandcamp.
Next month on December 6th, Devine will share the stage with Iszoloscope, Oddie(Orphx) & Creature at Foufounes Electriques in Montréal as part of AMP Industrial Events. Then on the 7th, we will both(remotely) present a summary of all the interesting analog communication schemes that inspired and found their way into Rabbit Waves and Wiktopher for Iterations 2024 organized by Creative Coding Utrecht.
Devine's talk for Handmade Seattle 2024 entitled A Shining Palace Built Upon the Sand was released online(YouTube), we also released the written transcript.
Due to the ongoing Canada Post strike we had to close the sale of stickers in our store, we'll let you know once we resume operations (this also applies to Patreon supporters, we'll ship perks your way as soon as we can).
Book Club: This month we are still reading The Memoirs of Sherlock Holmes by Arthur Conan Doyle.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of October.
Pino is back in Victoria. Being back in a city also means that we are shipping sticker sheets again! Devine found a spirograph set at a thrift store for 5$, we now make patterns on every letter we ship.
We are happy to announce the official release of Rabbit Waves! The idea for the project came after discussing the disappearance of certain traditional seasteading skills and maritime communication knowledge that we believe are valuable when electronics misbehave, but that are also just generally fun to learn and use. The world of the micro-site will grow as we think of new ideas to expand it.
Devine participated in Drawtober again this year and completed a zine that teaches the basics of multiset rewriting with examples, it also includes the source for a tiny Fractran interpreter. Since its release, many people have printed their own. Avanier went a step further and re-drew the zine on black paper! Devine also released an interactive version, and CapitalEx created with it a beautiful little world to explore! Handmade Seattle 2024 is coming up, Devine will be there to talk about weird computer stuff, and will hand out copies of the zine too.
This year, we carved a Calcifer pumpkin (see our other Halloween pumpkins).
Book Club: This month we read The Memoirs of Sherlock Holmes by Arthur Conan Doyle.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of September.
September started off warm, but got cold and windy fast, we spent lots of time sitting by the woodstove drinking tea. As promised, we have begun transcribing the Victoria to Sitka logbook digitally, we release one week's worth of logs at a time. We populated the logs with photos and Rek's sketches(also sourced from the handwritten logbook). End of the month, we closed our summer 2024 sailing route, Pino has traveled very far this year! We made 76(!!!) stops over a period of 5 months, sailing 1900 NM.
We announced a new project this month named Rabbit Waves. It will serve as a vessel to expand, in a playful way, on some of our favourite things. Expect lots of art featuring root vegetable root-shaped sailboats, rabbits, and seabirds! The website will host more content next month.
For 3 years now, we've had a monthly hand-drawn calendar in the galley that we cover with doodles, at the end of the year, Rek binds the 12 pages together, and it makes it easy to look back at where we were, what we were doing at a previous time. Everyday has some kind of highlight or other. It's one of our favourite habits.
Listen to Devine's remix of SOPHIE's One More Time feat. Popstar.
Book Club: This month we read Project Hail Mary by Andy Weir. We are forever in love with Rocky.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of August.
This month, Pino reached the northern tip of Vancouver Island, sailed south through Johnstone Strait, and into calmer, familiar waters on the 11th of August. Both of us were eager for a taste of summer weather, we hoped to catch what was left of it. Our legs demanded an anchorage with options for walking, so we chose to anchor in Hathayim Marine Park. The lovely people on the sailboat Nanamuk were anchored here too, they mapped many of the trails in the area, even the overgrown, less-traveled routes. We updated our summer route map through northern B.C.
From May 1st to August 11th, like with our book Busy Doing Nothing, Rek kept a detailed logbook of daily happenings onboard. We hope to publish these notes to this wiki soon.
Book Club: This month we are reading The Adventures of Sherlock Holmes by Arthur Conan Doyle, The Design of Everyday Things by Don Norman, and Everyday Utopia: What 2000 years of Wild Experiments Can Teach Us About the Good Life by Kristen R. Ghodsee.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of July.
Pino and crew have moved a lot in the past month. On the first of July, we were in Sitka, Southeast Alaska, and then on the last day of the month we were back in Millbrook Cove, very near to the top of Vancouver Island. We sailed 590 NM and stopped in 15 different anchorages.
Leaving Sitka, we sailed along the west coast of Southeast Alaska for a few days to try and take advantage of a good weather window, we had some engine issues which too motivated the need for such a long passage(see our track)—we spent two days troubleshooting the issue while anchored in Port Bazan, a bay far from everything, with no internet connection or way to talk to anybody, we were glad to have the physical engine manual on board. Sailing on open waters is always nice, we saw black-footed albatrosses, horned puffins, a whale per hour, and many more sea otters(Port Bazan was full of them).
After checking back into Prince Rupert, the way back south through Northern Canada was plagued with unfavorable winds, we had to beat into it, or travel on quiet waters to make progress. We resorted to doing short hops between anchorages, conditions did not permit for long distances. Doing short hops though did allow us to discover beautiful places we might have otherwise missed. We spent many grey days waiting for weather, reading, drawing, and beginning work on markl, we're giving it another go).
Book Club: This month we read Erewhon by Samuel Butler, Technophilia and Its Discontents by Ellen Ullman, The Democracy Of Species by Robin Wall Kimmerer, I Will Fight No More Forever by Merrill D. Beal, In Cold Blood by Truman Capote, and Mrs Dalloway by Virginia Woolf.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of June.
We spent all of June cruising through Southeast Alaska, we visited 4 cities and stopped by 14 different anchorages. On June 27th, 420 nautical miles later, we arrived in the beautiful town of Sitka — our favorite city so far.
We have sailed as far north as we are willing to go this year, at 57°N — the same latitude as Kodiak. Sailing in these waters has been challenging, there is a lot of current, and the wind is often light, or absent. Because of these frequent calms, Calcifer II has seen a lot of use this year. We will now slowly make our way back south, exploring new anchorages along the west coast of Southeast Alaska all the while. We continue to update our path in Alaska here, when we cross back into Canada we'll resume updates here.
Book Club: This month we are reading West With the Night by Beryl Markham.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of May.
We spent this month moving northward through both southern and northern British Columbia. We've been moving almost every day, stopping every night to anchor, sleep and recuperate. Sailing near land is not as relaxing as sailing offshore, this reef-strewn coast requires careful navigation. We've had many long days of endless tacking from one side of the channel to the other, almost all the way to Port McNeill, then after that we started to get more weather from the south for some mostly pleasant, but cold and rainy, downwind sailing. We've been using our woodstove a lot, in evenings it helps warm the boat after a long sail.
On May 29th, 623 nautical miles miles after leaving Victoria, we arrived in Prince Rupert, our last major port in British Columbia before we head north to Southeast Alaska. Then, on June 2nd, we arrived in Ketchikan, Southeast Alaska. Most of our updates this month detail some of the places we've been(see the above list). To see our path, look at Western Canada and us se alaska. We update the map as we find internet.
We've seen sea otters, lots of humpback whales, two pods of orcas(one pod had a baby tagging along), eagles, and lots of mountains. In other non-travel related news, Devine is going to speak again at Handmade Seattle this upcoming November!
Book Club: This month we are reading The Martian by Andy Weir.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of April.
Devine has been busy working on the implementation and documentation of wryl's fantastic programming language Modal. Rewriting systems are a computation paradigm that is generally unknown and under-explored that might have some fascinating features that might be able help us to tackle some of our future projects.
In other news, Pino is ready to head northward! We finished all of our boats projects and left the dock on May 1st. See a photo of our first day of the year on the water, taken as we exited Enterprise Channel, just north of Trial Island south of Victoria. On our travels we will continue to push updates every month like usual, but the updates will only go live when we find internet, and this may or may not coincide with the start of every month. We will keep a log of our travels, populated with plenty of drawings!
Book Club: This month we are reading The Fountainhead by Ayn Rand.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of March.
Pino now has all-new chainplates! We removed the original ones earlier this month to inspect them and found some pit corrosion(as well as a small crack), replacing them was necessary. With the chainplates gone, we removed the entire starboard side cabinet to see what was behind it—it's always nice to see parts of our boat we've never seen. We also replaced 3 old halyards on Pino. Devine earned themself a couple of blisters splicing dyneema onto some of our existing halyards.
Sejo revisited the Uxn tutorial, and appended corrections. The most important change is that the tutorial is now targeting the learn-uxn platform(online) maintained by metasyn. Now, people can jump right in and experiment without having to set up a dev environment. Tsoding, someone who can code in front of the camera in a language they've never used or read the docs for, did a pretty funny session in Uxntal, you can watch it here.
There has been too many exciting Uxn projects coming out these past few days, so we'll just put a link to the hashtag. Someone also created a Discord channel, it's a good place to learn about other concatenative languages and an alternative for people who have trouble with #uxn, in irc.libera.chat.
This month we are reading The Last Great Sea by Terry Glavin, and we watched the movie Tenet.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of February.
Late last month we started re-modeling part of our galley, the work is now complete! It's subtle, but the splash image for the log now includes the re-design. We will test our new galley when we go out cruising.
Pino will be adventuring a bit more north this summer, we're planning to explore the north coast of British Columbia, all the way to Prince Rupert, or possibly Ketchikan(AK), areas with little to no cell coverage. How far we go depends on what we find on the way. If the seas and winds are kind, and if we have time, we might go farther. We spend our days studying charts, gathering supplies, and fixing up the boat to make sure the passage is safe and pleasant. More updates on our plans soon!
Want to see something cool? Xsodect made Tetris(Mastodon) in Orca.
This month we watched The Race to Alaska Movie.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of January.
On January 10th the forge that we use to host our projects was taken down by DDoS attacks and was struggling to come back online(it's back now, read the post-mortem), the event reminded us that we ought to host mirrors and release versions of these source files ourselves. We have begun to host copies across our various websites. The builds are still accessible through itch.io. These will be automatically updated as we work on them in their individual repositories, but mirrored there for reliability. We are thankful for Sourcehut's tireless work on resolving the issue and for taking the time to communicate important changes.
In keeping with the spirit of improving the resilience of the tools we use we've taken a moment to write a kind of pocket version of the console emulator and self-hosted assembler as to see how many lines are needed to start from the seed assembler and replicate it. A copy of the pocket emulator, the source for the assembler and its hexadecimal representation have been documented.
On January 17th Victoria got its first snowfall, with it came temperatures below freezing. We got to test our recent improvements, like a new louvered closet vent to help ventilate the space(there are also two existing vents at the top, one on each side). The closet has been dry for the first time in 3 years. We've made an effort not to keep too many items on the floor so the area can breathe. We got ice inside of the windows for the first time ever though... not ideal.
See Uxn running on a Zaurus Husky(Mastodon).
This month we are reading The Haunting of Hill House by Shirley Jackson.
Hey everyone!
This is the list of all the changes we've done to our projects during the month of December.
Wiktopher was released on paperback! Our small collection of self-published books is growing.
We finished the upholstery in the saloon, Pino feels like a new boat. We also published an article on this past summer's Solar Cooking Experiment.
Last September Devine and a group of people went on a 3-day train ride from Seattle to St Louis for the last edition of Strange Loop 2023. This video documents that journey.
As mentionned in November's update, Tinyletter, the service we use to send out our monthly newsletter, is shutting down in February 2024. We will now be using Sourcehut to send our monthly updates. With this new system our emails will be leaner than ever, using plain text(no html). We cannot transfer accounts to this new list ourselves, so if you want to keep receiving updates by email please sign up again here. Clicking on the subscribe button will open your email client, you can leave the body and subject of the email blank. We will keep sending newsletters with TinyLetter until the end of January 2024, so as to give people time to make the switch. If you sign up to this new list, unsuscribe from the old newsletter to avoid getting two emails with the same content for December and January. We hope you continue to follow our updates.
Note that since it's our first time sending updates with the new newsletter format, it may look a little wonky. We'll improve on it next month.
2023 was kind to us, we look forward to seeing what 2024 brings! We hope the coming year treats you all well.
This month we are reading The Tartar Steppe by Dino Buzzati, and we went to see 君たちはどう生きるか(The Boy and the Heron).
Hey everyone!
This is the list of all the changes we've done to our projects during the month of November.
Wiktopher is finally finished. We started this book in 2017 while in French Polynesia, constrained by power limitations and hardware failures. Writing demanded less energy than drawing digitally, Rek could use the Chromebook to work (see tools ecosystem). You can read the first two chapters of the finished story here[4.1 MiB] as a PDF. If you liked what you've read, we hope you'll consider reading the rest!
We treated ourselves this month to new saloon cushions(see upholstery). We sleep and live on these, it's so nice to have plump cushions again!
IMPORTANT. You may have heard but the service we use to send our newsletter(TinyLetter) is shutting down early next year (Feb 2024). We are in the process of setting up an alternative, we'll provide details on that in December's newsletter and on this website.
We are reading Thomas Pynchon's The Crying of Lot 49, and enjoyed watching Close Encounters of the Third Kind.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of October. We'll also be reporting in our on position in the world, and on our future plans.
This month we got tattooed(Mastodon) by the very talented Lizbeth. Check out her tattoo art.
Devine's Strange Loop 2023 talk was released online, watch it here(YouTube). We also released the talk as a text version, Computing and sustainability, for those who prefer to read. We talked with the members of Frugarilla on their latest podcast(French), in which we finally admit that our whole thing is a sneaky way of getting programmers interested in food preservation.
Every year we carve halloween pumpkins, this year we made a Uxn pumpkin!
See Oquonie running on a linux handheld(Mastodon).
We are reading Selma Lagerlöf's The Wonderful Adventures of Nils.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of September. We'll also be reporting in our on position in the world, and on our future plans.
Pino returned to the Victoria docks a little early this year so Devine could go to Strange Loop 2023. We had a lovely sail that day, with clear skies, and 10 kts on the beam. Despite being a little food and sleep deprived, Devine's presentation went well, we will share the recording here once it is released.
Rek has been busy editing Wiktopher, finessing the conlangs featured in the story. One of the featured languages is Ilken, a whistled language, designed for long-distance communication, and playable with instruments. A few years ago Devine designed a language for it, but we decided to instead use a modern variation of Solresol, a musical language by Jean-François Sudre. Rek drew a fanart of the mascot of Solresol, and Devine a communication lantern.
Currently, Devine is working at translating Thousand Rooms(Famimi Remisolla) in Solresol as practice. We're also editing a Brazilian Portuguese version, to be released next month.
We've been toying with the idea of making an audiobook for the story, and asked Paul B. to use their voice synthesis tool Gesture to try and hear what a poem in Ilken(Solresol) sounds like. The result was so lovely that it made Rek cry of joy.
Rek's sketch thread(Mastodon) is still going. Devine will be producing a lot more art next month for Drawtober!
We are reading J.D. Salinger's Catcher in the Rye, and B. F. Skinner's Walden Two.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of August. We'll also be reporting in our on position in the world, and on our future plans.
Pino sailed a bit more northward this month and went all the way to the Octopus Islands. We visited this place during a very windy week, with winds blowing 30-35 kts the entire time. We got acquainted with a few northern rapids, like Hole in the Wall and Surge Narrows. It is a bit of a mindfuck to think that in these waters the tide ebbs north and floods south.
This summer has been especially arid, and because of it the province has seen a lot forest fires (see pictures of our smokey transit). Trails that we know and love on Cortes Island, that are usually wet and muddy, were bone dry this year. We had a few days of hard rain, during that time we collect rain water and go for walks to look for slugs and snails.
Both of us have been drawing a lot this month, see this Neoneve portrait(Mastodon) by Devine (drawn with Oekaki), and this sketch thread(Mastodon) by Rek..
We have read Adam Wisniewski-Snerg's Robot, George Orwell's Homage to Catalonia, and Michael A. Hiltzik's Dealers of Ligthning.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of July. We'll also be reporting in our on position in the world, and on our future plans.
We spent many quiet days in Roscoe Bay, and then wandered over to melanie cove for a few days before moving to our favorite anchorage in Desolation Sound, Hathayim Marine Park. This inlet is quiet, and not overly busy, it is ideal for focusing on projects. We walk the 3 km trail to Squirrel Cove everyday.
We have been hard at work reviewing Wiktopher, and we're happy to announce that we've finished the first pass of corrections! We'll be doing many more passes, but this was a very big step. Rek has been drawing(Mastodon) a lot, and Devine has been working on their presentation for Strange Loop 2023.
Check out this amazing Uxn cheat sheet by Nettie!
We are reading Lewis Carrol's Bruno and Sylvie. We re-watched Vampire Hunter D for the hundredth time.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of June. We'll also be reporting in our on position in the world, and on our future plans.
Pino spent the first few days of the month on land, having its bottom re-painted, and its various bits serviced and checked. We took our propeller apart for the first time.
We've added a few write-ups of our travels so far (see above entry with links under 100r.ca), but the most significant one is our 46nmi sail up to Princess Louisa Inlet, a long fjord on British Columbia's Sunshine Coast, with an incredible gem at the end. It is an amazing, and unique place. We're glad we finally got to go. As we write this, we are in Roscoe Bay on West Redonda Island, tethering off a phone hoisted up the mast (it works quite well).
This summer we are power stable. We had issues last year because of parisitic draws due to old wiring (see DC electrical refit), but now everything is working as it should. We're charging our computers without an inverter, and that too is working out quite well so far (see charging electronics).
Together, Hikari and Lynn made chibicc-uxn, a c compiler for Uxn, and with it also released a port of the classic software Neko(xneko, oneko sakura).
We are reading Arkady and Boris Strugatsky's Roadside Picnic. We've been re-watching Kaamelott(the series, book 1 though 6) for the hundredth time.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of May. We'll also be reporting in our on position in the world, and on our future plans.
Pino is off the dock, and spending time at anchor. The weather has been excellent, and with days of full comes sun solar cooking! We baked some bread, and roasted some green coffee beans in the sun. We are enjoying some quiet days before we haul the boat out of the water at the start of June.
Devine's talk proposal to Strange Loop 2023 has been accepted, so parts of the summer will be collecting our notes and writing slides for the presentation in September.
The recording for the show Devine(Alicef) did with Anju Singh and Reylinn(visuals) last march for Biosonic on Galiano Island is online, watch it here.
We had a small impromptu logo jam event on Merveilles this month. Members of the community re-interpreted the logo, with illustrations, photo collages, and even food. See all of the entries so far. Nf just completed Fourtette, a block game. Devine provided guidance, Rek made the title screen art, and d6 provided music.
We went to the theater for the first time in a long time, to see Suzume(2023). We have also finished reading Saint-Exupery's Courrier Sud.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of April. We'll also be reporting in our on position in the world, and on our future plans.
Oquonie is out and it is playable! A big thank you to those who helped us test the game on a variety of devices and systems all the way to Windows95. This version of Oquonie differs a little from the original, in that some of the puzzles and secrets have changed. We hope that those who played the original will too enjoy this one. We have a special build of the game on itchio with the emulator and rom combined, if you have a false-negative virus warning on Windows 10, you will need to use the standard uxn32 emulator and rom.
We have watched as people implemented their own emulators and were able to play Oquonie on a Varvara of their own making. The current implementation documentation might need to be improved, if you have feedback for things that could be clearer, please let us know!
We published our experiments with solar cooking this month, and wrote a more detailed post on solar evacuated tube cooking. The real test will happen this summer. We plan to keep a log of everything we cook, how long it takes, and the conditions(sun, overcast, temp etc).
We're still closing a few projects aboard Pino, to get it ready for some summer sailing. Our plans for now are loose, we're hauling the boat out of the water in early June, with plans to sail back towards Desolation Sound afterward, with a possible stop by Jervis Inlet.
We're watching La Belle Verte by Coline Serreau.
Hey everyone! This is the list of all the changes we've done to our projects during the month of March.
We spent the first half of March on Galiano Island in the Salish Sea for BioSonic(by ActivePassive), an event series exploring the intersections of music, art and biodiversity. On March 10th we gave a talk titled What Are Computers For?, see the art from the talk. The next day, Devine and Anju Singh performed together using Orca, with Reylinn on visuals. A video of the perfomance and of the talk will be released soon, in the meantime, see photos of the talk and of the show, taken by photographer Dayna Szyndrowski.
We are still working on re-releasing Oquonie. We spent the month of March playing the game, finding bugs, and fixing them. Oquonie will be playable next month.
This month we've been experimenting with solar cooking, to try to save on cooking fuel this summer. We are currently making tests, gathering data, and hope to share this with you all end of April. In the meantime, enjoy this amazing music by Xsodect, made using Orca.
We're reading Structure and Interpretation of Computer Programs (SICP) by Harold Abelson, Gerald Jay and Julie Sussman.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of February. We'll also be reporting in our on position in the world, and on our future plans.
On February 14th, we celebrated our 7th year living aboard our beloved Pino. It's also around this time 10 years ago that we were still living in Odaiba(Japan), and beginning our work on what would be our first game collaboration: oquonie.
The uxn port of Oquonie has advanced in incredible leaps this month. Rek has finished re-doing all of the assets. Devine is now working on the music, and finalizing some of the levels. We are testing the game as we go, and hope to release it sometime next month. Oquonie will be playable on a number of platforms, including the Nintendo DS(Mastodon), as well as the Playdate. See a small preview(Mastodon).
Early next month we are traveling to Galiano Island in the Salish Sea for BioSonic(by ActivePassive). We'll be part of an event series exploring the intersections of music, art and biodiversity. We'll give a talk on March 10th, and Devine will perform with Orca on the 11th at the Galiano South Hall.
Watch Devine's set for Lovebyte 2023.
We're reading Courrier Sud by Antoine de Saint-Exupéry.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of January. We'll also be reporting in our on position in the world, and on our future plans.
This month, we started porting Oquonie to Uxn. This is a long time coming, but we weren't sure if it was possible to do, and we still had a lot to learn before even thinking of taking it on. Now, we think we are ready. We are re-drawing the sprites(Mastodon), and they look amazing. This is an important test for us, and for Uxn.
Here is a very adorable little Uxn sprite for Potato that comes up when a rom path was mistyped, see it also on the Uxn page.
We're reading The Journey Home: Some Words in Defense of the American West by Edward Abbey.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of December. We'll also be reporting in our on position in the world, and on our future plans.
The rabbits are re-wiring Pino. So far this month, we spent entire afternoons removing, and passing new wires into the boat's walls and ceiling. This project has taken up most of our time this month. For updates on the project, see electrical refit. We also released an edited transcript of Devine's talk weathering software winter, for those who prefer to read.
We forgot to mention it in the last update, but Compudanzas just released a new version of their introduction to uxn programming book! The online tutorial also had some updates.
Happy new year everyone! See more photos of Pino(on the far left) and friends decorated for the occasion.
We're reading Le Péril Bleu by Maurice Renard.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of November. We'll also be reporting in our on position in the world, and on our future plans.
We put some red lights on Pino, to help combat winter gloom. We also started growing another lion's mane mushroom on board(we grew the same variety last fall), it already has a little tuft!
Devine's talk Weathering Software Winter for Handmade Seattle was recorded, watch it here(Vimeo). The video is for the entire first day of the conference, so for your convenience Devine's talk starts at 1h25min.
A little while ago Rostiger drew an amazing series of illustrations explaining Uxn, and how it works. Ben made a zine out of it and gave us a copy. Make your own Uxn zine using this PDF[1.38 MB].
We're reading Gulliver's Travels by Jonathan Swift, and How to Blow Up a Pipeline by Andreas Malm.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of October. We'll also be reporting in our on position in the world, and on our future plans.
Pino is in Victoria again, and we're diving back into our favorite fall activities like pumpkin carving (see halloween pumpkins), and fruit picking. The boat is now filled with apple jam. October was a drawing month for the both of us. Devine participated in drawtober and completed 28 drawings using Noodle. Rek finished a sequence for the ongoing comic project Hakum.
For those in the Pacific Northwest, Devine will be giving a talk called Weathering Software Winter at Handmade Seattle on November 17th.
As you know, we share a community online with a fantastic group of people. Some months ago Lizbeth designed a burgee for Merveilles and this month we decided to make one for Pino. See the Merveilles burgee.
We're reading Life, the Universe and Everything by Douglas Adams, and What The Doormouse Said by John Markoff.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of September. We'll also be reporting in our on position in the world, and on our future plans.
The days are getting shorter, and so is the time that we can spend on the computer, due to our batteries depleting earlier a bit each day. So, Devine spends evenings proof-reading the wiktopher manuscript, reading and messing around with the Playdate, and Rek continues ink work on an upcoming project(Mastodon, no project page yet).
While cleaning up the boat, Devine found two small black notebooks. We started paging through them, to see if we should keep them. The notebooks were full of sketches, interspersed with shopping lists, and incomplete logs from earlier sailing trips we'd done. We found logs detailing our very first attempt at sailing offshore, our sail down the US West Coast and Mexico, and our passage from Tonga to New Zealand. We read the logs, and decided to transcribe and publish them online. Read the lost logbook.
Devine wrote a little timer program for the Adafruit Playground.
We're reading Hitchhiker's Guide to the Galaxy by Douglas Adams.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of August. We'll also be reporting in our on position in the world, and on our future plans.
Pino is back in the land of faster internet, and our boat's belly has been re-filled with food. We returned to the Gulf Islands, and are busy eating as many wild blackberries as we can stomach ('tis the season).
Our last anchorage in Desolation Sound was Tenedos Bay, a really lovely place with an amazing (vertical) hike, and clear, clear waters. We also wrote a post on Sturt Bay on Texada Island, a place we stopped on the way up earlier this year, and again when we traveled back south.
As mentioned brieftly in our last post, Devine has been working on an OS called Potato. Rek drew a mascot, and another illustration featuring Varvara and Potato together. Potato is for the Varvara computer, designed to fill the gaps where a host device might not have an underlying file system, like handheld consoles (many people use Uxn on Nintendo DS).
Rek has been drawing a lot, their winter will consist of scanning and processing a sketchbook-full of art. We are still proofreading Wiktopher. A recent stop in Sidney permitted us to print the entire book on paper to make it easier (and more pleasant) to make corrections. The result is 70 (double-sided) pages of text. As of today, we have gone over and marked in red the first chapter (out of 12). Editing books is never easy or fast, but we'll get there.
We know a couple of people have made hako dice sets, so we feel bad for "patching" a physical game, but the face organization of the die has changed somewhat, now, the opposing sides are always of equal value. If any of you are looking for a simple 2-player boardgame to play, try Conway's Phutball. Devine transcribed the rules on their wiki.
We're reading Mathematical Puzzles & Diversions by Martin Gardner.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of July. We'll also be reporting in our on position in the world, and on our future plans.
Sometimes we find an anchorage that is so nice, so ideal, that we end up staying for weeks. We stayed in Von Donop Bay (hathayim marine park) for well over a month. The southernmost anchorage is near many trails that snake and branch out deep into the woods, and the bay is so large that we kept finding new corners to explore by dinghy. The water in the area is warmer than in Victoria, we can dive, and check Pino's bottom without freezing. This is our first real summer on the boat, when we have no big boat projects to do, nor big transits to plan, and it feels amazing.
We have stretched our food stores to the limit (it has been 2 months since we last stocked up in full). A 5 km trek through the woods takes us to a little General Store, they never have fresh produce (or it gets bought out before we get there) but we go once in a while to replenish our stock of potatoes and onions. We are relying on sprouts a lot (see growing food).
This month, we made a Keynote talk for Nime 2022, and Devine started work on a little OS project called Potato, see some footage(Mastodon). There is no documentation yet, but soon.
We're reading The Stories of Ray Bradbury by Ray Bradbury.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of June. We'll also be reporting in our on position in the world, and on our future plans.
Pino is currently in Desolation Sound, enjoying the quiet. We've written a few posts about some of the anchorages we've visited, like melanie cove, grace harbour and hathayim marine park. We're updating our track as we go.
Devine has been adding a lot of notes to the permacomputing wiki this month. We also started a little arcade game named Inle, something that we could play together on the boat in the style of Gunbound/Tank Wars... but with rabbits (we finished reading Watership Down last month, so we blame that, haha). We don't have a project page yet for it, but we shared some images on the post for grace harbour, where we started working on the game.
Rek produced a video about image optimization for the Photographer's Gallery (as part of their Green Hacks video series) last month.
We're reading The Man who Mistook his Wife for a Hat by Oliver Sacks.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of May. We'll also be reporting in our on position in the world, and on our future plans.
From this month until next October, our updates may be delayed. We are sailing northward, towards Desolation Sound and the Broughtons, where cell towers are few. We will wander in and out of such regions all summer. So far, we sailed up to the Gulf Islands, and over to Nanaimo from Victoria, and then crossed the Strait of Georgia over to the Sunshine Coast(close-reaching in 20-knot winds). This was a good shakedown for Pino, a good way to re-awaken our little vessel. All went well, but we ought to have secured our produce better... some of our potatoes escaped their nest and went out for an afternoon roll around the cabin floor.
Start of May, we had some issues with our batteries. They've been acting out for some time, we think because of a dead cell. We have been operating at half battery capacity for a month, and realized that yet again we don't need that much power, especially in the summer when the days are long.
The combinatory logic guide is the first of many projects we plan to release this summer. We also released an sign language version of Uxntal.
In other news, a version of Collapse OS was ported to Uxn.
We're reading Watership Down by Richard Adams.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of April. We'll also be reporting in our on position in the world, and on our future plans.
The month of April was a time of boat projects. We built a mini dodger to cover the companionway, and installed a large spindle for floating rope on Pino's stern (marine stores give those spindles away for free, usually). In these waters, it is often necessary to stern tie to shore when anchoring and the spindle will make it easier to uncoil the line.
We also took some time off to visit some ancient trees in Cathedral Grove on Vancouver Island.
Devine found some slide rules and wrote a guide on how to use them.
If you want to play Catpot, the little Hypercard game we made for Merveilles Hyperjam 2020, you can play it with this Hypercard Simulator (thank you Dan).
We're reading The Stranger by Albert Camus.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of March. We'll also be reporting in our on position in the world, and on our future plans.
A major update to our wiki is that we've put together a text with our stance on various political aspects. Because of the decentralized nature of some of our work, and because of the overlap of libertarians and right-wing doomsday preppers and our documenting survivalism at sea, there were things that just had to be spelled out quite clearly. See philosophy. We've appended a notice to our off the grid page too, since it gets shared the most.
A lot of our time this month was dedicated to preparing for our keynote talk for LibrePlanet 2022 called Software Doldrums. If you missed it the talk was recorded, watch it here. Rek illustrated all of the slides for the presentation, gathered here. These images are now scattered on our wiki. Devine built the Uxn slideshow program Adelie for that presentation, we plan to use it again for all future talks.
The day prior, Devine gave a short performance(YouTube) for Algorave's 10-year anniversary, alongside over 140+ artists. The event was 24 hours, with everyone playing a 10-minute set.
Uxn was featured on The Verge, in an article entitled These artists are making tiny ROMs that will probably outlive us all. And Devine was interviewed(Medium) for Behind the Screens.
In other news, we finally made some Uxn sticker sheets!
We're reading We Have Always Lives in the Castle by Shirley Jackson.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of February. We'll also be reporting in our on position in the world, and on our future plans.
This month it was announced that we joined LibrePlanet 2022 as keynote speakers. The annual technology and social justice conference will be held virtually on March 19 and 20, 2022, with the theme Living Liberation. Our talk is named Software Doldrums.
Rek is putting the finishing touches to Wiktopher, and Devine designed a game that the people of Irideri could be playing. The result was a dice game combining the capture mechanism of Go and the randomness of the Domino. Learn to play Hako. Each player has a Sonozai, a set of 4 dice on a rope. Merveillans have been making their own sets:
Rostiger has been making illustrated notes for Uxn, and they are fabulous.
We're reading Underland by Robert Macfarlane.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of January. We'll also be reporting in our on position in the world, and on our future plans.
On January 28th Uxn turned 1 year old! We'd like to thank everyone who has contributed code, ideas, time and laughs to help this project grow into what it is now. It was a wonderful year for smol ordinators. See an image that Rek made for uxn's birthday.
We finally released versions of the Uxn emulator for all major systems(Linux, OS X and Windows), with the option of a version bundled with a few starter roms. We simplified the guide too, to make it easier to install and use.
Our lion's mane mushroom grew another full head, we harvested it and made some mushroom pakoras.
In other news, Devine was interviewed on Anonradio, listen to it here. Also, Compudanzas released an Introduction to Uxn Programming book, with a foreword by Devine.
We're reading The Complete Cosmicomics by Italo Calvino, and The Dawn of Everything: A New History of Humanity by David Graeber.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of December. We'll also be reporting in our on position in the world, and on our future plans.
It is snowing, and we are cocooning. Our little woodstove is working hard. This month, we finally decided to release a paperback version of Busy Doing Nothing.
In our last update log, we mentioned that we were trying to grow Lion's Mane mushroom, and we are happy to report that it was a success! It grew beautifully. Rek was so excited about the mushroom that they decided to draw some this month, this series focuses on varieties that grow on Vancouver Island.
In other news, we had an interview with the founder of Sourcehut, read it here. Also, our good friend Alderwick make us a very cool gift(YouTube).
We're reading Fantômes: Issue 1, with work by 18 talented artists, put together by Lizbeth. It is a eerie, and gorgeous zine, we strongly recommend the Mike Wolf version.
Pino's location: 48° 42.230'N, 123° 36.900'W
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of November. We'll also be reporting in our on position in the world, and on our future plans.
This month, there was an intro to Uxn Programming(YouTube) workshop by Compudanzas, an event by Babycastles Academy. Give it a watch!
November was a very rainy month in Victoria, a perfect time for experiments in the galley. We are growing Lion's Mane mushrooms currently (a first for us), and we are continuing to lacto-ferment vegetables like kohlrabi, turnips, daikon, cauliflower and red onion. To learn how to do it, see our guide to lactofermentation.
We're reading The Summer Book by Tove Jansson (it's such a lovely book).
Pino's location: 48° 42.230'N, 123° 36.900'W
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of October. We'll also be reporting in our on position in the world, and on our future plans.
This month, we found a used grain mill for Pino! Flour doesn't keep as well as whole grains, so we decided to start milling flour (wheat berries, soy beans or chickpeas) only as we need it. We only released a Guide to Lacto-fermenting vegetables on grimgrains.
Donsol is now available as an uxn rom on itchio.
See Devine's daily drawings series for October.
We're continuing our readings of The Stories of Ray Bradbury by Ray Bradbury. Favorite shorts this month include The Long Rain, The City and Kaleidoscope.
Pino's location: 48° 42.230'N, 123° 36.900'W
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of September. We'll also be reporting in our on position in the world, and on our future plans.
It is an early announcement, but end of June 2022 we will be giving a keynote presentation, alongside Khyam Allami, at NIME(New Interfaces for Musical Expression).
Rek wrote an article on Saving Energy When Cooking Aboard for Noonsite.
Check out Eli's guide on installing Uxn on OS X, and Keijiro's version of Flappy Bird in UxnTal.
Our friends at Compudanzas have released part 6 of their Introduction to Uxn Programming tutorial. This new chapter basically shows you how to build Pong!
We started reading The Stories of Ray Bradbury by Ray Bradbury. Favorite shorts so far include There Will Come Soft Rains, The Coffin and There Was an Old Woman.
Pino's location: 48° 42.230'N, 123° 36.900'W
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of August. We'll also be reporting in our on position in the world, and on our future plans.
This month, our little engine was fixed (read about it here) we've been sailing around the Gulf Islands, working from anchor. We also found Iggy's successor, a used fiberglass dinghy that we've named Teapot. We've been rowing it from ship to shore, and it's so, so nice. We stopped by Saltspring Island and got to meet the sailors on BosunBird, a couple who have traveled around the world on a Vancouver27. Their blog was an invaluable resource for us on our travels through Japan.
We've released a solid version of noodle, our drawing tool. Follow the tutorial on our website, or check out this amazing quick start guide by Polyducks. We also released niju, our little kana-learning game. Niju was a trial to see if we could design, write and assemble a project entirely within the Uxn computer.
Our friends at Compudanzas have released part 3, 4 and 5 of their Introduction to Uxn Programming tutorial.
Help. We still haven't finished The Swarm by Frank Schatzing. It is terrible, but we can't stop.
Pino's location: 48° 53.370'N, 123° 23.734'W
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of July. We'll also be reporting in our on position in the world, and on our future plans.
This month, Calcifer is being re-built. While we wait for that, we're working on more projects aboard. We added insulation to the v-berth, an attempt to keep Pino warm this winter. We created a new portal called boat projects on our wiki that covers most of the major construction projects we've done to the boat.
Our friends at Compudanzas have started writing an Introduction to Uxn Programming tutorial. We recommend it to anyone interested in programming for the Uxn Computer. No prior understanding of stack-machines, or Assembly, required! The first covers basics, and the latest chapter focuses on learning to draw pixels on the screen.
If you missed Devine's performance at Flash Crash, you can watch it here.
We're reading Mingming & the Art of Minimal Ocean Sailing by Roger Taylor and The Swarm by Frank Schatzing.
Pino's location: 48° 40.768'N, 123° 24.802'W
The work is done. Building a dry toilet was more work than we had anticipated, but we still prefer it over the ready-made models. We learned tons doing it, and now our toilet is perfectly suited to our space. The pandemic has pushed more people into boat and van living (to travel within their own countries) and towards simple systems. Looking at the Nature's Head website, they've had a 8-week waiting list for ages. It's either you wait for the thing, or you build the thing.
Dry toilets are simple to use and have few parts, but it doesn't mean that they are simple to build. Simple is hard, it costs time, and requires a ton of creativity.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of June. We'll also be reporting in our on position in the world, and on our future plans.
Pino and crew spent the first half of the month in the boatyard. We splashed back into the water on the 14th and moved to North Saanich to have access to a workshop with the goal of completing our dry toilet. We are documenting the entire installation, with plans to update the page when we begin to use it. We are ALMOST done with this project.
We started working on Niju, a hiragana/katakana review application. We used this project to test our the latest iteration of Nasu so we could finalize the documentation.
On June 26 2021, Devine met up with the London SF reading group to talk about solarpunk, see their notes. On July 10th UTC 20:00, Devine will also perform with Orca for flash crash.
See Uxn running on the ESP32. It is TOO adorable!
We're reading Nature as Measure by Wes Jackson, The Strange Last Voyage of Donald Crowhurst by Nicholas Tomalin and Ron Hall and Labyrinths by Jorge Luis Borges.
Pino's location: 48° 40.768'N, 123° 24.802'W
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of May. We'll also be reporting in our on position in the world, and on our future plans.
There has been a lot of activity on Uxn this month! It's exciting to see it work on a variety of devices, like the PS vita, Gameboy Advance and the Nintendo DS. We love the idea that most people already have the all hardware necessary to run our software.
We hosted a small cooking jam on Merveilles, feel free to peruse The Galley tag to see the recipes.
In Pino related news, we are moving north. First stop, the boatyard. We'll be doing a bunch of changes to the studio this week, like removing and replacing old thru-hulls and installing a dry toilet.
We're reading Farenheit 451 by Ray Bradbury.
Pino's location: 48° 40.768'N, 123° 24.802'W
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of April. We'll also be reporting in our on position in the world, and on our future plans.
This month, we converted the old static version of our website into a wiki, with pages for each of the various projects we've been working on aboard Pino. We hope you like it!
We also finished installing our wood stove. Our timing could have been better (it's summer now), but we'll be able to keep warm while at anchor next winter. We have many projects to do, including the removal and replacement of many thru-hulls and plumbing, as well as the installation of a dry toilet. Looks like Pino will have to come out of the water again this year!
We're reading Terre des Hommes by Antoine de Saint-Exupéry and Sylvie and Bruno by Lewis Carroll.
Pino's location: 48° 42.230'N, 123° 36.900'W
It was our dream to have a little wood stove aboard Pino. After researching stoves, we decided that the best model was the cast iron Sardine from Navigator Stoveworks.
Our Espar forced air diesel heater broke on our last passage, and we decided not to replace it. There are few low-power alternatives to a gas/diesel heater for heating a boat when off the grid. A wood stove was our best low-tech option. We also like that it doubles as a cook top...
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of March. We'll also be reporting in our on position in the world, and on our future plans.
This month, the rabbits have been busy making new holes in Pino, cutting metal, and building a support platform for their new tiny woodstove. When the installation is complete, we have plans to write a blog post about the process.
If you're seeing this update on the 100r.ca website, you'll notice that all logs are now in the same file. It is easier for us to manage, and we think, more pleasant for you to read.
We have received a lot of really good feedback and corrections for our book Busy Doing Nothing, thank you for reading it. Rek has updated their notes on creating e-books with Pandoc to include exports to epub and mobi (for those interested).
We're reading The Complete Rigger’s Apprentice by Brion Toss and Thinking Forth by Leo Brody.
Pino's location: 48° 42.230'N, 123° 36.900'W
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of February. We'll also be reporting in our on position in the world, and on our future plans.
This month, we released the e-book version of the North Pacific Logbook titled Busy Doing Nothing. The book is 217 pages long, and is available as a PDF, mobi or EPUB. We're happy it's out, and hope that you like it!
In other news, Esoteric.Codes interviewed our studio, and we heard that the Toronto Public Library was hosting an online Orca workshop on March 1st—how cool is that?
We're reading A Sand County Almanac by Aldo Leopold.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of January. We'll also be reporting in our on position in the world, and on our future plans.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of December. We'll also be reporting in our on position in the world, and on our future plans.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of November. We'll also be reporting in our on position in the world, and on our future plans.
Hey everyone! This is the list of all the changes we've done to our projects and apps during the month of October. We'll also be reporting in our on position in the world, and on our future plans.
Our traveling studio has operated off-the-grid for 4 1/2 years.
For the first 3 years we tested the limits of our space, and at first, it was difficult to create new things, as we had to make time to learn how to solve underlying problems. Our boat was not just an office, it was also our house and transport. As for us, we were artists, but also plumbers, deckhands, electricians, captains, janitors and accountants.
Our main problems as a studio were internet scarcity, power management, data storage as well as hardware and software failures. Overtime we found ways to balance work, pleasure and maintenance. Here are some of the lessons we learnt.
The passage from Japan (Shimoda) to Canada (Victoria) took 51 days, and it was the hardest thing we've ever done. We decided to keep a logbook, to better remember it and so it can help others who wish to make this trip.
For every traveling sailor, comes a time when the boat has to stay alone in a foreign country. For us, this happened this year in Japan. We'd never left Pino alone before, never for more than a week. We were apprehensive at first, but decided it would be a good learning experience, for us and our beloved.
Whenever we mentioned leaving our boat in Japan, people would say, 'Aren't you afraid of typhoons?' Our 6 month leave coincided with the time of year when typhoons affect Japan, with August to October being the worse months. We were worried, but knew that if we prepared well, Pino would be fine. We spent weeks planning our departure, doing research on how to keep a boat safe in a storm, but also, how to keep mold and insects at bay in our absence.
While in Canada, I had anxiety at night, vivid dreams about what was happening to Pino. These dreams involved us returning to the boat, only to find it turned into a moldy, water-logged cockroach motel. Having no experience leaving our home behind, I had no guarantee that we had done enough.
When we returned 6 months later, we found no mold, no bugs and little to no damage, in fact, we slept in that same night. Pino endured weeks of hot Japanese summers, tropical rain and typhoon-strength winds. We're happy to say that overall, our preparations were indeed enough.
Below is a short list of things to remember, things we learned, when came time to prepare our boat for long-term storage:
We left Shimizu on a sunny morning, pushing off the dock at 6am. Early. We wanted to make sure we'd arrive at our destination on time. There was 126nm between us and Shima Yacht harbor, a distance we needed to do in part at night. This wasn't ideal. We knew that. Many people warned us about sailing at night in these waters, but as the Japanese say: 'Shoganai' (it is what it is!). We needed to cross a big stretch of water called Enshu Nada, an area with a lot of traffic. In truth, the entire coastline is full of ships, but it gets very busy north of the Kii Peninsula.
We left Shimizu on a sunny morning, pushing off the dock at 6am. We discussed our plans with our friends Masa and Shu from Dawntreader, they too recommended a non-stop trip because the ports between Omaezaki and Mie are few. There is the port of Fukuda 福田, located at the mouth of Ota Kawa, but the depth of the water is inconsistent and prone to silting. Locals also warned us it wasn't very yacht-friendly, and so we put an X on Fukuda.
Shu instructed us to stay 10nm from shore, to avoid the many nets lining the coast, and to avoid small fishing vessels idling there at night. We did as told.
Coming out of Shimizu port, we came face to face with a large container ship named 'One'. A beautiful ship. Red, with a peculiar shape. The marina had warned us about its coming, that its entrance into Shimizu port was scheduled at 6am during our exit. Avoiding it was not a problem.
We powered out of the harbor and into Suruga Bay. There was no wind, but we raised the mainsail anyway. We wanted to test our new slugs (what keeps the mainsail attached to the mast). It was the first time since Fiji that we'd raised a full main. The black moon shook off its wrinkles, presenting its belly to the sun.
How did the Hundredrabbits ecosystem come into being? It's a long story, but here's a summary.
In 2016, we left Canada, armed with our two iPhones and 2 MacBooks Pros. We didn't know the wattage of any of the devices we owned, and even less about the amount of solar needed to power them. When living on land we didn't pay attention to how many amps our devices required daily. Electricity felt limitless.
When we started sailing in BC, we had no dinghy and so we'd go from dock to dock. When we purchased Iggy in Nanaimo, we spent more days on the hook. The first anchorage we went to was a small bight east of Eagle Point, it offered a great view of metro Vancouver. From that point on we spent more and more time at anchor, moving every 5 days or so. We had no power concerns because our route always included marinas, or guest slips at yacht clubs. Our batteries were always topped up.
Life off-grid was new to us then, as was spending lots of time outdoors. We liked it, a lot. When at anchor we'd go explore, spend a few hours working, cooking, then we'd read or play card games in evenings. When living on land, we'd work from 8h-19h, sitting in front of our respective screens, but now things were different. We wanted to do less of that, to take long bike ride around islands or to sit on the deck in evenings to watch the sun set. Then, at marinas where we had both power and internet, we'd go back to working longer hours to get things done. This was a fine setup, we thought, but, there was problem: what happens when we start living AND working at anchor full time? We liked being outdoors, but that's not all we wanted to do. We're creatives, and we need to make things. We were relying on powered docks to work, and so we never got to test our current power setup off-grid. If we had spent a month or so away from civilization, we would have learnt that we had to change something.
And so, to continue with the story, we left Canada and cruised down the coast of the US. True to our old habits, we continued to alternate between staying in a marina and at anchor. The longest we spent off-grid during that time was 3 weeks in San Francisco, anchored off Treasure Island. During that time we discovered that working aboard, running two Macbook Pros, a refrigerator and our phones was not possible. To save on power, we started turning the fridge off at night, and taking trips into town during the day to work from cafes. SF was grey on most days, our solar couldn't keep up with our demanding work schedules. Going to work from cafes in town worked well for us, most had outlets we could use. Our routine started with working from cafes until lunch, then wandering around in the afternoons. We would return home before dark to turn the fridge off, but doing it didn't make sense because the constant shifts in temperatures produced too much moisture. Moisture meant rot and mold. We decided that keeping it off was a better idea for both our batteries and our produce. With the fridge out of the equation, we figured that we'd have more power left-over for our laptops.
It's 8h00 pm on a cold dark winter night, we are outside of Shimizu harbor motoring in circles and waiting for a response from Shimizu Port Control. The temperature is 4 °C, the wind is blowing hard and our clothes are wet and caked with salt. We’re tired and hungry, waiting for permission to enter the Port. Prior to this, we had a rough 4-day passage, riding under 30-40 knot winds on the nose. This passage was a true test of strength, for us and for Pino... but first, let’s go back and see exactly what happened…
We'd planned to go to Wakayama, riding on the back of a passing low with winds from the NE, shifting to the S and then to the SW, but the wind decided to turn earlier making it impossible for us to go east. We found ourselves close-reaching in 40 knot winds, heading straight north. Looking at the weather we could see that it would blow from the W for 3-4 days, so we made a new plan to head to Omaezaki. We'd read of other sailors taking refuge there in big weather and thought it would be possible to go, but again, the wind kept pushing us further and further east. The next port on our list was Shimizu, tucked in deep into the bay. We were able to point Pino to the cape just past Shimizu, but we weren't sure if again the wind and current would allow us to make some easting.
At that point both of us were frozen solid. Wave after wave splashed over the boat and into the cockpit. The starboard rail was constantly submerged, our starboard side lee cloth was gone and the diesel bins were threatening to fall overboard. We had 3 reefs in our main, but 5 slides had snapped off (yet again), I wondered when the rest would break.
After a long 21-day passage, seeing the shape of the island of Chichijima in the distance was unreal; this was our prize, our first step onto Japanese soil. We used to make many trips to Japan by plane, but getting there by our own efforts — by sailboat — is a lot slower and harder. If we had stuck to our plan of sailing there via Hawaii, we would have been there sooner, but I’m glad we took the long route. We passed through 9 countries, learned a lot about the world and, through it all, we've surpassed ourselves.
During that time, we often talked about what it would be like to arrive in Japan, about what would happen when we did. You have to remember that this was a big deal for us, a milestone in our lives and the culmination of 3 years of hard work. A fantasy made real is a hell of an achievement. A part of me couldn’t believe we’d made it — anytime now I’d wake up mid-ocean in transit in the South Pacific. Even when I’d have my feet planted on the ground, with a Japanese flag flying above my head, I knew I’d be anxious, waiting for something horrible to happen that would rob us of our victory.
'They’ll turn us away.', 'We’ve landed on the wrong island.' or 'We died in the pacific some months ago, and this is limbo.'
My eyes were set on the phantasmic island ahead. The sun fell out of the sky then, drawing down a star-studded curtain; the wind blew itself out, leaving the sea to settle into an unmoving and creepy oil slick. Limbo.
A bright circle appeared on the horizon then. It isn’t the first or the last time that I mistake the moonrise for a ship, or the bright eye of some mythological beast.
At this point, it looked like we’d be entering Futami port at night, but at least we had the eye of Sauron to light the way. The island in the distance stopped being a vague black patch, and we began to see details in it.
As soon as we'd tied to our mooring ball in Majuro's lagoon, the worries of the previous 24 days had vanished only to replaced by the crushing weight of responsibility. Devine, being worry-free, wanted to have pancakes, sleep and check-in tomorrow, but Devine knows how uptight I am, and that this was not what we'd be doing first (even if it is what I wanted too *sigh*). My thinking was that I'd rather get the paperwork out of the way first, to get all of that worrying out of me so I can then eat pancakes in peace.
We needed to be presentable for the officials, we had to wear clean clothes with pants that reach over your knees. A lot of countries in the pacific don't want to see your knees — I get it, knees are weird. We dug out some clothes from our bins, and then went back on deck to give Iggy the dinghy the kiss of life.
Here we go again, time for another passage. We left Fiji on October 23rd 2018, eager to spend some time on the water again. Our plan, was to stop by Tuvalu, maybe Kiribati, before arriving in Majuro in the Marshall islands where we'd be spending two months before moving off west to Micronesia. We left, knowing that this was wasn't going to be an easy ride...
Two areas of calms lie north of Fiji: the SPCZ (south pacific convergence zone) and the ITCZ (intertropical convergence zone). If you look at windy, hovering around the countries of Tuvalu and Kiribati are two bands of blue - blue means there is no wind. The size and location of these bands varies from day to day, week to week.. they phase in and out of existence with the weather and influence of the trade winds.
Sailors fear these blue bands because the weather there is difficult, not only do you suffer calms, but also a continuous ballet of squalls and thunderstorms. We've been through the doldrums (the ITCZ) once already when we crossed from Mexico to the Marquesas.
We've never been on a tiny island, a place you can run the width of under just a few minutes. We found a place like this, Leleuvia, an island in the Lomaitivi archipelago in Fiji.
This island went through many hands over the years, it now belongs to a resort that too bears the name of the island. We decided to make a stop there on our way to Suva, to wait for favorable winds to go south.
Also, we wanted a taste of tiny-island living.
We arrived at Moturiki pass around 1pm. SY Scoots gave us a number to phone the resort on arrival, so they could send a boat to guide us through the reef. We realized then, that our phone plan didn't include calls within Fiji, all we had was data — woops! That's ok! We still had the option of calling them on VHF. I hailed them repeatedly on CH10 — no luck.
I had waypoints for the entrance, but not all the way to the anchorage. Many areas in Fiji aren't charted well, you can find yourself navigating over an area with the depth sounder reading '10m' but the chart will display a patch of green, an area too shallow to pass. It's always disconcerting, to find yourself anchored in a patch of green, like sitting in a negative space, a secret place that you didn't think existed.
We got closer and closer to the green area, growing ever-so nervous, and continuing to try and hail the resort. Eventually, they picked up my call.
We wouldn't be entering the anchorage in the blind after all. We would have eyes to guide us to a safe spot.
We motored on, nearing the pier, and spotted the escort boat. The driver came within shouting range, instructing us to follow, which we promptly did. They led us to a mooring, and assured us it was strong and that it could take our weight — not that Pino is heavy. We grabbed the line from the water, with a bit of difficulty, sometimes the mooring 'eye' for the buoys are submerged, and you need to figure out which bit to grab to get to it. We missed the mooring ball the first time, the whole endeavour was made worse by the up and down motion of the bow — there was a bit of swell coming into the anchorage from the north at the time. We rounded again to grab the mooring ball, i spied a thin loop at the top of the ball, and thrusted the boat hook in it. I hurriedly pulled the float out of the water, and my hands and the line found the mooring loop. This is not my favorite type of mooring ball, where you need to pull the ball up itself to find the rope hanging far underneath it, usually they'll put a separate float on the line to keep it buoyant. All moorings are different.
The northerly swell would stop soon, the forecast called for 20-25kts out of the SE tomorrow. On the chart, the area looked protected from swell, with a reef belt around it, but looking around now, aside from the tiny spit of land that is Leleuvia, there was only water. At low tide the reef became evident, as the water receded sand banks came into view, fencing us in from all directions but from the North. Phew. The reef would break most of the waves, but at high tide some swell would make it past it for sure — not ideal, but we would have some protection.
The next day the wind did freshen, and as expected, at high tide the waves spilled into the anchorage. It was bumpy, but not overly so.
Pino spent a long time in Savusavu, but by then, we were growing tired of this scenery, not of the market, or of the company to be found here, but just of having that same view every morning. We love this city, but when it's time to go, it's time to go!
We left our mooring at 9am, and moved along over to Cousteau's resort to anchor (16 48.623S, 179 17.331E). The water was unclear, and the clouded sky made it difficult to see bommies beneath us. Devine dove in and checked out our anchor, which was set in sand, and we weren't near any huge coral that we could see, that is, unless the wind shifted - it was hard to see that far in cloudy water to be honest.
SV Privateer arrived shortly after us, having made the short passage by sail, we saw them manoeuver around, looking for a place to drop the hook.
They hovered around some more, opening the headsail, furling it, in and out again, and moving the main in and out to make their way around the anchorage. It's always impressive to watch, not many will rely on wings alone to do this. They'll do as many tacks as necessary to get where they need to go - engines be damned!
We tried swimming at the beach that afternoon, but it was full of seaweed and unclear, we much preferred staying on the tiny slab of beach lining the shore to watch the hundreds of tiny hermit crabs moving about. They were different sizes, wearing a grand variety of shells - some spirally, others conical, stained with purples and whites, oranges and cream. We sat there in silence, listening to the sound of their shells rubbing against bits of broken coral. Such a pleasant sound, small scratching noises. Crkk, crkk... crkk.
We left our hermit crab friends behind, and went back aboard Pino. Tomorrow morning we had to get up at 4am to sail to Makogai (pronounced ma-kon-guy), 49NM away.
The wind changed in the night, we could hear the chain rubbing against bit of coral, catching, before coming off again with a jerk, the sound traveling to us by the chain through the hull. We should have probably buoyed the chain, we thought then, but it was dark, and too late to think of doing this now. Hopefully, the chain wouldn't have this macramé thing going on with the bits of coral down there.
We arrived in New Zealand with a long scary list of things to fix or replace on Pino. We needed new batteries, a new mainsail, a fresh coat of bottom-paint, galley plumbing, new intermediates shrouds, new backstay, new top hatch, new windows, new control cables etc.
That was the deal. There was too much ocean between us and Japan. Our vessel needed to be made safe to endure it, and to ensure our safe passage.
When we landed in the country, we had grand ideas, 'grand illusions' I should say, about what we thought we could get done by ourselves. We wanted to learn, but we also wanted to save money. By now, we knew how much it cost to offload the work to others, and it's not something we knew we could do.
Below, is a detailed account of all the repairs we did on Pino during the 9 months we spent in New Zealand. This is a technical post, interspersed with bits of story, present and past. For those who don't know the terms, but that are interested, I'll do my best to explain them all throughout the text.
Here I go!
Traveling to New Zealand, after a year of unknown, was a great comfort to us. There are a few things Devine and I were really looking forward to, like a good latte, craft beer, a fresh food market and a bulk food store. I found a city that checked all of the boxes.
Many of the cruisers we know want to arrive in Opua – with reason. It's warm, damn gorgeous, and you know you'll find friends there, because that's where everyone goes during the cyclone season. Arriving in a strange place, with familiar faces, always makes the experience better, but knowing this, we still chose Whangarei.
I first pronounced Whangarei as 'one-gah-rey', but the proper way to say it is: 'fah-ngah-rey'. A friend corrected me early on, sparing me the embarrassment of mispronouncing it aloud in public. I know that no one would think me a fool for making a mistake like this, but I do like learning the correct way to say things.
Why did we choose to go there? Because staying in the Whangarei Town Basin is inexpensive, convenient, with everything just a short walk away. We'd also read that it was a good place for boat projects, and since Pino needed a lot of attention, this too, we thought, tipped the scale in its favor. We also noted that it was close to Auckland — well, it looked closer on a map. We became very familiar with that stretch of land, and of the actual distance between the two places during the 8 months we spent there.
The first thing we did when we arrived, was to replenish our store of dried goods at Bin Inn, a really great bulk food store. The second thing, was purchasing a home brew kit - priorities amirite? The third thing, was to get a latte.
I'll never forget the look on Devine's face after taking a sip of a cup of freshly brewed beans, a delicious pool of dark liquid topped with a pillowy cloud of plant milk.
Joy incarnate.
After 15 days on the water, we were to get into port. It was the 27th of June, and we'd left Opua on the 12th. We hove-to for the night, waiting for sunrise before entering Savusavu bay. 'Entering a strange harbor at night is for morons and fools,' people told us. We didn't listen right away, but they were right. In this particular case, there was no point in arriving early, considering yachts cannot anchor in Fiji waters before checking in, and that check-in is only possible after 8am.
At dawn, we pointed towards the island of Vanua Levu and sailed on, with the wind at our backs. I went below to make some coffee, as both of us needed a boost. Devine was in the cockpit, keeping an eye on a large storm cloud ahead. The wind increased as we neared it, but it did not trouble us long. We made our way inside the reef, which offered some protection from the building swells, and moved closer to land. We could see rows of hills ahead, and caught the perfume of greenery. After that, came a sure sign of civilization: buildings, low, with green and red roofs. As we got nearer, came an even more obvious sign of civilization: cars, and small power boats. We'd arrived.
We neared the entrance to Nakama creek around 9am, and radio'ed the authorities on channel 16.
I hailed them 3 times, no answer. We slowed down, awaiting a reply. The commercial wharf lay ahead, we could see boats on moorings, some abandoned, others belonging to people we'd seen or met accross the Pacific. Eventually, they replied and asked us about the details of our trip, and if we had sent a pre-arrival notice. Sending it ahead of time was mandatory, and was about 10 pages too long. I'd sent it to the proper people by email, although half of the messages bounced back, and other cruisers reported the same thing happening. With the document being so large, it's no wonder their inboxes are always full. I even tried sending it again while underway, no luck. No matter. I'd received a reply from the custom office, at least one of the messages made it. They told us to look for a white building on our starboard side.
Niue, pronounced 'New-ay', a rock in the Pacific, one of the largest coral islands on earth. It's the first country to offer free, state-funded, wireless internet to all its residents and has a goal of being completely solar powered— uuuh... wow?
We'd also heard that the school gave all of the kids laptops, this, with free internet, makes it a paradise for people like us. Already then, we made plans to move there — like all places in the tropics with a good connection and supply of coconuts and beer. I remember when we were speaking of staying in Nuku Hiva too, and in La Paz. We make a home everywhere we go. This, makes it hard to leave, but this ease of adaptation also makes us eager to go forward, to see where else we could live. This is what we do, we set up house in different places, sometimes for 8 months at a time.
We weren't going to be staying long in Niue though, but not by choice.
Alofi Bay, the only anchorage on the island, is not protected in any wind other than east. If the wind turns in an unfavorable direction, staying could be dangerous and we'd be forced to leave.
One other troublesome thing about the 'rock of Polynesia', is that they hiked the departure fees from 35$ to 80$ per person. Anyone who enters Niue, when leaving, need pay this fee. That's a lot of money, we thought, to visit a place so small.
In the end I'm glad we went, because of all the places we'd been, Niue was our favorite.
We arrived at 6am in the morning, rounding the island to Alofi bay that lay on the west side. A squall lay between me and the anchorage, a puffy cloud with a thick wet skirt. I pulled my hood on, grabbed the helm firmly and quickly skipped through songs on my phone till I landed on anything by Purity ring. Ah! Sea castles. Yes, perfect.
WOOSH! A gust of wind comes, but I'm ready. The song begins then too... 'I could build a machine—' The boat heels, '—draw pictures for the walls.' Then comes the rain, heavy droplets, washing the salt crystals away. It left as quickly as it came, giving way to the sun, its face reflected in a thousand wet pools on the deck. 'Hang up all my fragile frights—' I point Pino towards the anchorage. Tall masts ahead, signs of life. The water, a deep blue, spotted with brightly-colored floaters. '—Display that you may see.' I sing aloud, turning the music off. 'We're here!' I shout to Devine.
Huahine, one of the many grouped islands in French Polynesia. Our plans for future ocean voyaging could have ended here, because we almost crashed onto a reef.
Because we always time our arrival with the morning sun, I always get the first look of every island. Huahine stood in front of us, a series of volcanic peaks marked by deep valleys and blanketed in green, an island that came into being million of years ago.
We were heading for Baie d'Avea, to the south of the island.
Nuku Hiva, a green mountainous island in the Pacific, straight out of Jurassic Park. Just as foreign and just as wild, except instead of hungry lizards there are mosquitoes, also known as the vampires of the Marquesas.
Before arriving, we didn't know what it was going to be like there, we'd barely read anything about it. We knew where we'd anchor, that people there spoke french and that there would be tropical fruit, but beyond that it was a blur, a black spot in our minds. We read the book Fourteen during our 28-day transit from La Paz. In this book, the family sailed to Nuku Hiva, but their experience there was not so good. It wasn't bad because of the Marquesans, or the island itself, but because of no-no's, little biting bugs that hide in sand. We took a mental note of this: "Avoid sand beaches, and you will have a great time!"
On day 27 of our voyage, I could see the outline of the island in the distance. I stood at the bow, trying to take footage of the event, but was disappointed with the shot. Far-away wonders have a way of looking unimpressive on camera. I was about to put the camera away, when I heard a 'wooshing' sound. I looked over the side, and saw an orca whale swimming next to Pino, its length matching our own. It stayed with us for a long while, it's white belly making it easy to spot it in the water. This unusual encounter was a great start to our Marquesian adventure.
Pino arrived at the entrance to Taiohae bay. I sat on the bow with Iggy's deflated corpse. I pumped life back into it, while it, sucked mine out. I was sweaty, a constant stream of body water oozing down my back. We had no dinghy pump, having broken it ages ago. All we had was a jury-rigged contraption using a bike pump, a bike tube and the hose from the old pump. It worked, but it took twice as long to put air into anything.
A super yacht was anchored in the mouth of the bay, called 'Ethereal'. "How fitting", I thought.
It's as if the yacht was a sign, a warning of the view to come — one, that was definitely ethereal.
A chain of mountains, green and fuzzy, and ahead a bay filled with boats flying flags from all over the world. We found a spot in 12 m of water, mud bottom, and dropped anchor. The sky was clear, but clouds clung to the peaks of every mountain. It was a rare thing, we realized afterwards, for the skies to be clear. Most days were grey. While grey often means rain, it also means less sun. It was over 30 degrees every day, so hot that at times we couldn't work, our bodies shiny with sweat, driving us mad. Mad to the point that we seriously considered flooding the cockpit with water to turn it into a pool.
What if the music charts you see aren’t real? What if the numbers that define success can be manufactured? We talked to Andrew, a man who has spent his career on both sides of this battle. He once profited from the loopholes in streaming platforms, but now, his job is to close them. This episode will change the way you understand music streaming platforms from now on.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Support for this show comes from Adaptive Security. Deepfake voices on a Zoom call. AI-written phishing emails that sound exactly like your CFO. Synthetic job applicants walking through the front door. Adaptive is built to stop these attacks. They run real-time simulations, exposing your teams to what these attacks look like to test and improve your defences. Learn more at adaptivesecurity.com.
This episode is sponsored by Meter, the company building networks from the ground up. Meter delivers a complete networking stack - wired, wireless, and cellular - in one solution that’s built for performance and scale. Alongside their partners, Meter designs the hardware, writes the firmware, builds the software, manages deployments, and runs support. Learn more at meter.com.
Phrack is legendary. It is the oldest, and arguably the most prestigious, underground hacking magazine in the world.
It started in 1985 and is still running today. In this episode we interview the Phrack staff to hear some stories about what it’s like running a hacker magazine for 40 years.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Support for this show comes from Drata. Drata is the trust management platform that uses AI-driven automation to modernize governance, risk, and compliance, helping thousands of businesses stay audit-ready and scale securely. Learn more at drata.com/darknetdiaries.
This episode is sponsored by Meter, the company building networks from the ground up. Meter delivers a complete networking stack - wired, wireless, and cellular - in one solution that’s built for performance and scale. Alongside their partners, Meter designs the hardware, writes the firmware, builds the software, manages deployments, and runs support. Learn more at meter.com.
Legion of Doom, step aside. There’s a new elite hacker group in town, and they’re calling themselves Masters of Deception (MoD). With tactics that are grittier and more sophisticated than those of the LoD, MoD has targeted high-profile entities and left an indelible mark on the internet.
This is part 2 of the LoD/MoD series. Part 1 is episode 168: “LoD”.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
This show is sponsored by Red Canary. Red Canary is a leading provider of Managed Detection and Response (MDR), helping nearly 1,000 organizations detect and stop threats before they cause harm. With a focus on accuracy across identities, endpoints, and cloud, we deliver trusted security operations and a world-class customer experience. Learn more at redcanary.com.
This show is sponsored by Maze. Maze uses AI agents to triage and remediate cloud vulnerabilities by figuring out what’s actually exploitable, not just what’s theoretically risky. They remove the noise, prioritize vulns that matter, and manage remediation, so your team stops wasting time on meaningless vulns. Visit MazeHQ.com/darknet for more information.
The Legion of Doom (LoD) wasn’t just a “hacker group”, it captured the essence of underground hacking in the 80s/90s. BBSes, phreaking, rival crews, and the crackdowns that changed everything. From those humble beginnings came a legacy that still echoes through modern security culture today.
This is part 1 of the LoD/MoD saga. Part 2 is episode 169: “MoD”.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
This show is sponsored by Rippling. Rippling is the unified platform for Global HR, Payroll, IT, and Finance. They’ve helped millions replace their mess of cobbled-together tools with one system designed to give leaders clarity, speed, and control. With Rippling, you can run your entire HR, IT, and Finance operations as one, or pick and choose the products that best fill the gaps in your software stack. Learn more rippling.com/darknet.
This show is sponsored by Meter, the company building networks from the ground up. Meter delivers a complete networking stack - wired, wireless, and cellular - in one solution that’s built for performance and scale. Meter’s full-stack solution covers everything from first site survey to ongoing support, giving you a single partner for all your connectivity needs. Go to meter.com/darknet to book a demo now!
A manufacturer gets hit with ransomware. A hospital too. Learn how Threatlocker stops these types of attacks. This episode is brought to you by Threatlocker.
This episode is sponsored by ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Maxie Reynolds loves an adventure, especially the kind where she’s breaking into buildings (legally). In this episode, she shares stories from her time as a professional penetration tester, including high-stakes physical intrusions, red team chaos, and the unique adrenaline of hacking the real world.
Her book: The Art of Attack: Attacker Mindset for Security Professionals (https://amzn.to/4ojYSVZ)
Her data center: www.subseacloud.com/
Tanya Janca is a globally recognized AppSec (application security) expert and founder of We Hack Purple. In this episode, she shares wild stories from the front lines of cybersecurity. She shares stories of when she was a penetration tester to an incident responder.
You can sign up for her newsletter at https://newsletter.shehackspurple.ca/
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
This episode is sponsored by Hims. Hims offers access to ED treatment options ranging from trusted generics that cost up to 95% less than brand names to Hard Mints, if prescribed. To get simple, online access to personalized, affordable care for ED, Hair Loss, Weight Loss, and more, visit https://hims.com/darknet.
Support for this show comes from Drata. Drata is the trust management platform that uses AI-driven automation to modernize governance, risk, and compliance, helping thousands of businesses stay audit-ready and scale securely. Learn more at drata.com/darknetdiaries.
He started small, swiping cards, buying gift cards, and cashing out. It spiraled into a full‑blown criminal enterprise. Dozens of co‑conspirators, stacks of stolen plastic, and a lifestyle built on chaos.
Meet Nathan Michael, leader of Oak Cliff Swipers.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Support for this show comes from Pantheon. Pantheon keeps your site fast, secure, and always on. That means better SEO, more conversions, and no lost sales from downtime. But this isn’t just a business win; it’s a developer win too. Your team gets automated workflows, isolated test environments, and zero-downtime deployments. Visit Pantheon.io, and make your website your unfair advantage.
Support for this show comes from Adaptive Security. Deepfake voices on a Zoom call. AI-written phishing emails that sound exactly like your CFO. Synthetic job applicants walking through the front door. Adaptive is built to stop these attacks. They run real-time simulations, exposing your teams to what these attacks look like to test and improve your defences. Learn more at adaptivesecurity.com.
In 2019, Ola Bini, a Swedish programmer and privacy advocate, was arrested in Ecuador for being a Russian hacker.
Find Ola on X: https://x.com/olabini. Or visit his website https://olabini.se/blog/. Or check out his non-profit https://autonomia.digital/.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
This show is sponsored by Miro. AI doesn’t have to be intimidating—in fact, it can help your team thrive. Miro’s Innovation Workspace changes that by bringing people and AI together to turn ideas into impact, fast. Whether you’re launching a new podcast, streamlining a process, or building the next big thing, Miro helps your team move quicker, collaborate better, and actually enjoy the work. Learn more at https://miro.com/.
This show is sponsored by Thales. With their industry-leading platforms, you can protect critical applications, data and identities – anywhere and at scale with the highest ROI. That’s why the most trusted brands and largest banks, retailers and healthcare companies in the world rely on Thales to protect what matters most – applications, data and identities. Learn more at http://thalesgroup.com/cyber.
All Hieu Minh Ngo wanted was to make money online. But when he stumbled into the dark web, he found more than just opportunity, he found a global dark market. What started as a side hustle turned into an international crime spree.
Find Hieu on X: https://x.com/HHieupc.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Support for this show comes from Drata. Drata is the trust management platform that uses AI-driven automation to modernize governance, risk, and compliance, helping thousands of businesses stay audit-ready and scale securely. Learn more at drata.com/darknetdiaries.
This show is sponsored by Red Canary. Red Canary is a leading provider of Managed Detection and Response (MDR), helping nearly 1,000 organizations detect and stop threats before they cause harm. With a focus on accuracy across identities, endpoints, and cloud, we deliver trusted security operations and a world-class customer experience. Learn more at redcanary.com.
In this episode we talk with mg (https://x.com/MG), the brilliant (and notorious) hacker and hardware engineer behind the OMG Cable. A seemingly ordinary USB cable with extraordinary offensive capabilities.
Learn more about mg at: o.mg.lol
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Support for this show comes from Axonius. Axonius transforms asset intelligence into intelligent action. With the Axonius Asset Cloud, customers preemptively tackle high-risk and hard-to-spot threat exposures, misconfigurations, and overspending. The integrated platform brings together data from every system in an organization’s IT infrastructure to optimize mission-critical risk, performance, and cost measures via actionable intelligence. Covering cyber assets, software, SaaS applications, identities, vulnerabilities, infrastructure, and more, Axonius is the one place to go for Security, IT, and GRC teams to continuously drive actionability across the organization. Bring truth to action with Axonius. Learn more at axonius.com.
Greg Linares (AKA Laughing Mantis) joins us to tell us about how he became the youngest hacker to be arrested in Arizona.
Follow Greg on Twitter: https://x.com/Laughing_Mantis.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
This show is sponsored by Red Canary. Red Canary is a leading provider of Managed Detection and Response (MDR), helping nearly 1,000 organizations detect and stop threats before they cause harm. With a focus on accuracy across identities, endpoints, and cloud, we deliver trusted security operations and a world-class customer experience. Learn more at redcanary.com.
This show is sponsored by Miro. AI doesn’t have to be intimidating—in fact, it can help your team thrive. Miro’s Innovation Workspace changes that by bringing people and AI together to turn ideas into impact, fast. Whether you’re launching a new podcast, streamlining a process, or building the next big thing, Miro helps your team move quicker, collaborate better, and actually enjoy the work. Learn more at https://miro.com/.
Joe Tidy investigates what may be the cruelest and most disturbing cyber attack in history. A breach so invasive it blurred the line between digital crime and psychological torture. This story might make your skin crawl.
Get more from Joe linktr.ee/joetidy.
Get the book Ctrl + Alt + Chaos: How Teenage Hackers Hijack the Internet (https://amzn.to/3He7GNs).
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
This show is sponsored by Red Canary. Red Canary is a leading provider of Managed Detection and Response (MDR), helping nearly 1,000 organizations detect and stop threats before they cause harm. With a focus on accuracy across identities, endpoints, and cloud, we deliver trusted security operations and a world-class customer experience. Learn more at redcanary.com.
MalwareTech was an anonymous security researcher, until he accidentally stopped WannaCry, one of the largest ransomware attacks in history. That single act of heroism shattered his anonymity and pulled him into a world he never expected.
Support for the show comes from Black Hills Information Security. Black Hills has a variety of penetration assessment and security auditing services they provide customers to help keep improve the security of a company. If you need a penetration test check out www.blackhillsinfosec.com/darknet.
Support for this show comes from Arctic Wolf. Arctic Wolf is the industry leader in security operations solutions, delivering 24x7 monitoring, assessment, and response through our patented Concierge Security model. They work with your existing tools and become an extension of your existing IT team. Visit arcticwolf.com/darknet to learn more.
Support for this show comes from Cloaked, a digital privacy tool. Cloaked offers private email, phone numbers, and virtual credit card numbers. So you can be anonymous online. They also will remove your personal information from the internet. Like home address, SSN, and phone numbers. Listeners get 20% off a Cloaked subscription when they visit https://cloaked.com/darknet. Calling 1-855-752-5625 for a free scan to check if your personal information is exposed!
Grifter is a longtime hacker, DEF CON organizer, and respected voice in the infosec community. From his early days exploring networks to helping shape one of the largest hacker conferences in the world, Grifter has built a reputation for blending deep technical insight with a sharp sense of humor.
Learn more about Grifter by visiting grifter.org.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Support for this show comes from ZipRecruiter. ZipRecruiter has solved the hiring problem. Employers prefer it the most for so many reasons. Let’s start by telling you about their matching technology. They work hard to find the best candidates for your needs, and will instantly show you results once you post a job listing. ZipRecruiter will speed up your hiring process. See it for yourself at www.ziprecruiter.com/DARKNET.
This show is sponsored by Material Security. Your cloud office (think Google Workspace or Microsoft 365) is the core of your business, but it’s often protected by scattered tools and manual fixes. Material is a purpose-built detection and response platform that closes the gaps those point solutions leave behind. From email threats to misconfigurations and account takeovers, Material monitors everything and steps in with real-time fixes to keep your data flowing where it should. Learn more at https://material.security.
The dark web is full of mystery. Some of it’s just made up though. Chris Monteiro wanted to see what was real and fake and discovered a hitman for hire site which took him on an unbelievable journey.
Chris Monteiro Twitter: x.com/Deku_shrub, Website: https://pirate.london/
Carl Miller Twitter: https://x.com/carljackmiller.
Kill List podcast: https://wondery.com/shows/kill-list/
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
This episode is sponsored by ProjectDiscovery. Tired of false positives and falling behind on new CVEs? Upgrade to Nuclei and ProjectDiscovery, the go-to tools for hackers and pentesters. With 10,000 detection templates, Nuclei helps you scan for exploitable vulnerabilities fast, while ProjectDiscovery lets you map your company’s perimeter, detect trending exploits, and triage results in seconds. Get automation, accuracy, and peace of mind. First-time users get one month FREE of ProjectDiscovery Pro with code DARKNET at projectdiscovery.io/darknet.
This episode is sponsored by Kinsta. Running an online business comes with enough headaches—your WordPress hosting shouldn’t be one of them. Kinsta’s managed hosting takes care of speed, security, and reliability so you can focus on what matters. With enterprise-level security, a modern dashboard that’s actually intuitive, and 24/7 support from real WordPress experts (not chatbots), Kinsta makes hosting stress-free. Need to move your site? They’ll migrate it for free. Plus, get your first month free when you sign up at kinsta.com/DARKNET.
In this episode, we delve into the multifaceted career of Joe Grand, also known as “Kingpin.” A renowned hardware hacker and computer engineer, Joe has been exploring and manipulating electronic systems since the 1980s. As a former member of the legendary hacker collective L0pht Heavy Industries, he has significantly contributed to the cybersecurity landscape. Joe is also the proprietor of Grand Idea Studio, a research and development firm, and has shared his expertise through various media, including his YouTube channel. Join us as we explore Joe’s unique perspective on hacking, engineering, and his extraordinary journey in the world of technology.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Support for this show comes from Lumen. It used to be hard to track your metabolism, but Lumen is a little device that you breath into which tells you if your burning fat or carbs, fast and easy and have your results in seconds. And knowing that will help you know what kind of food your body needs. And knowing that will help you with your health goals like losing weight or gaining muscle. Take the next step to improving your health go to lumen.me/darknet.
Support for this show comes from ZipRecruiter. ZipRecruiter has solved the hiring problem. Employers prefer it the most for so many reasons. Let’s start by telling you about their matching technology. They work hard to find the best candidates for your needs, and will instantly show you results once you post a job listing. ZipRecruiter will speed up your hiring process. See it for yourself at www.ziprecruiter.com/DARKNET.
Conor Freeman (x.com/conorfrmn) stole money online. Lot’s of it. In this episode we talk with him, and hear how he did it, why he did, and what he spent it on.
Conor’s website: https://conorfreeman.ie
Conor’s X: https://x.com/conorfrmn
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Support for this show comes from Drata. Drata is the trust management platform that uses AI-driven automation to modernize governance, risk, and compliance, helping thousands of businesses stay audit-ready and scale securely. Learn more at drata.com/darknetdiaries.
Support for this show comes from ZipRecruiter. ZipRecruiter has solved the hiring problem. Employers prefer it the most for so many reasons. Let’s start by telling you about their matching technology. They work hard to find the best candidates for your needs, and will instantly show you results once you post a job listing. ZipRecruiter will speed up your hiring process. See it for yourself at www.ziprecruiter.com/DARKNET.
Have you ever got your bike stolen? In this episode we dive into the world of stolen bikes. Who does it and where do the bikes go? We talk with Bryan from Bike Index who investigates this.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
This show is sponsored by Flashpoint. As one of the largest private providers of threat intelligence, Flashpoint delivers what security teams need most: clarity. By combining cutting-edge technology with the expertise of world-class analyst teams, their Ignite platform gives organizations instant access to critical data, expertly analyzed insights, and real-time alerts —all in one seamless platform. To access one of the industry’s best threat data and threat intelligence, visit flashpoint.io today.
Jarett Dunn, AKA StaccOverflow, stole millions of dollars from a website called Pump Fun, and he wanted to do it in the most dramatic and theatrical way he could. His big heist is known as the “Stacc Attack”.
He has a merch store now freestacc.io.
Support for this show comes from Cobalt Strike. Cobalt Strike simulates real-world, advanced cyber attacks to enable red teams to proactively evaluate an organisation’s security readiness and defence response. Their Command and Control framework gives red teamers the ability to customise their engagements and incorporate their own tools and techniques, allowing you to stress-test specific parts of your incident response capabilities. Learn more about Cobalt Strike and get a custom demo at https://cobaltstrike.com/darknet.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Chris Rock is known for being a security researcher. But he’s also a black hat incident responder. He tells us about a job he did in the middle east.
https://x.com/chrisrockhacker
Sponsors
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Flare. Flare automates monitoring across the dark & clear web to detect high-risk exposure, before threat actors have a chance to leverage it. Their unified solution makes it easy to rapidly identify risks across thousands of sources, including developers leaking secrets on public GitHub Repositories, threat actors selling infected devices on dark web markets, and targeted attacks being planned on illicit Telegram Channels. Visit http://try.flare.io/darknet-diaries to learn more.
In Episode 20 of Darknet Diaries, we heard from Greg aka “mobman” who said he created the sub7 malware. Something didn’t sit right with a lot of people about that episode. It’s time to revisit that episode and get to the bottom of things.
Sponsors
This show is sponsored by Shopify. Shopify is the best place to go to start or grow your online retail business. And running a growing business means getting the insights you need wherever you are. With Shopify’s single dashboard, you can manage orders, shipping, and payments from anywhere. Sign up for a one-dollar-per-month trial period at https://shopify.com/darknet.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Sources
https://www.youtube.com/watch?v=GDMc2PZM4V4
https://www.illmob.org/notmymobman/
https://darknetdiaries.com/episode/20
In this episode we hear EvilMog (https://x.com/Evil_Mog) tell us a story about when he had to troubleshoot networks in Afghanistan. We also get Joe (http://x.com/gonzosec) to tell us a penetration test story.
Sponsors
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Ever wondered how far a fan would go to get a sneak peek of their favorite artist’s unreleased tracks? In this episode, we uncover the audacious story of some teens bent on getting their hands on the newest dubstep music before anyone else.
Sponsors
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
In this episode, Geoff White (https://x.com/geoffwhite247) tells us what happened to Axie Infinity and Tornado cash. It’s a digital heist of epic proportions that changes everything.
This story comes from part of Geoff’s book “Rinsed” which goes into the world of money laundering. Get yours here https://amzn.to/3VJs7pb.
In this episode, Joseph Cox (https://x.com/josephfcox) tells us the story of anom. A secure phone made by criminals, for criminals.
This story comes from part of Joseph’s book “Dark Wire” which you should definitely read. Get yours here https://www.hachettebookgroup.com/titles/joseph-cox/dark-wire/9781541702691.
Shannen Rossmiller wanted to fight terrorism. So she went online and did.
Read more about her from her book “The Unexpected Patriot: How an Ordinary American Mother Is Bringing Terrorists to Justice”. An affiliate link to the book on Amazon is here: https://amzn.to/3yaf5sI.
Thanks to Spycast for allowing usage of the audio interview with Shannen.
Sponsors
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Rachel Tobac is a social engineer. In this episode we hear how she got started doing this and a few stories of how she hacked people and places using her voice and charm.
Learn more about Rachel by following her on Twitter https://twitter.com/RachelTobac or by visiting https://www.socialproofsecurity.com/
Daniel Miessler also chimes in to talk about AI. Find out more about him at https://danielmiessler.com/.
Sponsors
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
Jim Browning has dedicated himself to combatting scammers, taking a proactive stance by infiltrating their computer systems. Through his efforts, he not only disrupts these fraudulent operations but also shares his findings publicly on YouTube, shedding light on the intricacies of scam networks. His work uncovers a myriad of intriguing insights into the digital underworld, which he articulately discusses, offering viewers a behind-the-scenes look at his methods for fighting back against scammers.
Jim’s YouTube channel: https://www.youtube.com/c/JimBrowning
Sponsors
Support for this episode comes from NetSuite. NetSuite gives you visibility and control of your financials, planning, budgeting, and of course - inventory - so you can manage risk, get reliable forecasts, and improve margins. NetSuite helps you identify rising costs, automate your manual business processes, and see where to save money. KNOW your numbers. KNOW your business. And get to KNOW how NetSuite can be the source of truth for your entire company. Visit www.netsuite.com/darknet to learn more.
This episode is sponsored by Intruder. Growing attack surfaces, dynamic cloud environments, and the constant stream of new vulnerabilities stressing you out? Intruder is here to help you cut through the chaos of vulnerability management with ease. Join the thousands of companies who are using Intruder to find and fix what matters most. Sign up to Intruder today and get 20% off your first 3 months. Visit intruder.io/darknet.
This show is sponsored by Shopify. Shopify is the best place to go to start or grow your online retail business. And running a growing business means getting the insights you need wherever you are. With Shopify’s single dashboard, you can manage orders, shipping, and payments from anywhere. Sign up for a one-dollar-per-month trial period at https://shopify.com/darknet.
CLAIM=a6e199f5f9fd5954e532117c829c8f0a8f0f1282=CLAIM
Axact sells fake diplomas and degrees. What could go wrong with this business plan?
Sponsors
Support for this episode comes from NetSuite. NetSuite gives you visibility and control of your financials, planning, budgeting, and of course - inventory - so you can manage risk, get reliable forecasts, and improve margins. NetSuite helps you identify rising costs, automate your manual business processes, and see where to save money. KNOW your numbers. KNOW your business. And get to KNOW how NetSuite can be the source of truth for your entire company. Visit www.netsuite.com/darknet to learn more.
Support for this show comes from ThreatLocker®. ThreatLocker® is a Zero Trust Endpoint Protection Platform that strengthens your infrastructure from the ground up. With ThreatLocker® Allowlisting and Ringfencing™, you gain a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker® provides Zero Trust control at the kernel level that enables you to allow everything you need and block everything else, including ransomware! Learn more at www.threatlocker.com.
This show is sponsored by Shopify. Shopify is the best place to go to start or grow your online retail business. And running a growing business means getting the insights you need wherever you are. With Shopify’s single dashboard, you can manage orders, shipping, and payments from anywhere. Sign up for a one-dollar-per-month trial period at https://shopify.com/darknet.
The #1 crime which results in the biggest financial loss is BEC fraud. The #2 crime is pig butchering. Ronnie Tokazowski https://twitter.com/iHeartMalware walks us through this wild world.
Sponsors
Support for this episode comes from NetSuite. NetSuite gives you visibility and control of your financials, planning, budgeting, and of course - inventory - so you can manage risk, get reliable forecasts, and improve margins. NetSuite helps you identify rising costs, automate your manual business processes, and see where to save money. KNOW your numbers. KNOW your business. And get to KNOW how NetSuite can be the source of truth for your entire company. Visit www.netsuite.com/darknet to learn more.
Support for this show comes from Drata. Drata streamlines your SOC 2, ISO 27001, PCI DSS, HIPAA, GDPR & many other compliance frameworks, and provides 24-hour continuous control monitoring so you focus on scaling securely. Listeners of Darknet Diaries can get 10% off Drata and waived implementation fees at drata.com/darknetdiaries.
This show is sponsored by Shopify. Shopify is the best place to go to start or grow your online retail business. And running a growing business means getting the insights you need wherever you are. With Shopify’s single dashboard, you can manage orders, shipping, and payments from anywhere. Sign up for a one-dollar-per-month trial period at https://shopify.com/darknet.
Madison's nude photos were posted online. Her twin sister Christine came to help. This begins a bizarre and uneasy story.
This is the story of D3f4ult (twitter.com/_d3f4ult) from CWA. He was a hacktivist, upset with the state of the way things were, and wanted to make some changes. Changes were made.
Sponsors
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this show comes from Quorum Cyber. Their mantra is: “We help good people win.” If you’re looking for a partner to help you reduce risk and defend against the threats that are targeting your business — and especially if you are interested in Microsoft Security — reach out to Quorum Cyber at www.quorumcyber.com/darknet-diaries.
Sources
https://www.vice.com/en/article/z3ekk5/kane-gamble-cracka-back-online-after-a-two-year-internet-ban
https://www.wired.com/2015/10/hacker-who-broke-into-cia-director-john-brennan-email-tells-how-he-did-it/
https://www.hackread.com/fbi-server-hacked-miami-police-data-leaked/
https://archive.ph/Si79V#selection-66795.5-66795.6
https://wikileaks.org/cia-emails/John-Brennan-Draft-SF86/page-7.html
This episode is about scammers in the Punjab region. Tarun (twitter.com/taruns21) comes on the show to tell us a story of what happened to him. Naomi Brockwell (twitter.com/naomibrockwell) makes an appearance to speak about digital privacy.
To learn more about protecting your digital privacy, watch Naomi’s YouTube channel https://www.youtube.com/@NaomiBrockwellTV. And check out the books Extreme Privacy (https://amzn.to/3L3ffp9) and Beginner’s Introduction to Privacy (https://amzn.to/3EjuSoY).
Sponsors
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from SpyCloud. It’s good practice to see what data is getting passed around out there regarding you, your employees, your customers, and your business. The dark web is a place where this data is traded and shared. SpyCloud will help you find what out there about you and give you a report so you can be aware. Then they’ll continuously monitor the dark web for any new exposures you should be aware of. To learn more visit spycloud.com/darknetdiaries.
Support for this show comes from ThreatLocker. ThreatLocker has built-in endpoint security solutions that strengthen your infrastructure from the ground up with a zero trust posture. ThreatLocker’s Allowlisting gives you a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker provides zero trust control at the kernel level. Learn more at www.threatlocker.com.
A new type of mercenary spyware came on the radar called Predator. It’ll infect a mobile phone, and then suck up all the data from it. Contacts, text messages, location, and more. This malware is being sold to intelligence agencies around the world.
In this episode we hear from Crofton Black at Lighthouse Reports who spent 6 months with a team of journalists researching this story which was published here: https://www.lighthousereports.com/investigation/flight-of-the-predator/.
We also hear from Bill Marczak and John Scott-Railton from Citizen Lab.
If you want to hear about other mercenary spyware, check out episodes 99 and 100, about NSO group and Pegasus. To hear another episode about Greece check out episode 64 called Athens Shadow Games.
Sponsors
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Support for this show comes from Akamai Connected Cloud (formerly Linode). Akamai Connected Cloud supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Team Xecuter was a group involved with making and selling modchips for video game systems. They often made mods that allowed the video game system to rip games or play pirated games. It was a crowd favorite in the modding scene. Until it all fell apart. The story of what happened to Team Xecuter must be heard to believe.
This episode features Gary Bowser. You can find more about Gary here:
https://twitter.com/Bowser_GaryOPA
https://garyopa.com/
https://www.gofundme.com/f/garyopa-restarting-his-life?utm_location=darknetdiaries
Sponsors
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this show comes from ThreatLocker. ThreatLocker has built-in endpoint security solutions that strengthen your infrastructure from the ground up with a zero trust posture. ThreatLocker’s Allowlisting gives you a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker provides zero trust control at the kernel level. Learn more at www.threatlocker.com.
Sources
https://www.washingtonpost.com/archive/politics/1994/10/27/ringleader-pleads-guilty-in-phone-fraud/56e551bb-a727-43e8-a3ca-1c1f4cf6ef82/
https://www.justice.gov/sites/default/files/usao/legacy/2010/10/12/usab4304.pdf
https://www.eurogamer.net/nintendo-to-appeal-not-guilty-judgement-of-flash-cart-sellers-7
https://www.gamesindustry.biz/nintendo-pounces-on-global-piracy-outfit
https://www.justice.gov/opa/pr/two-members-notorious-videogame-piracy-group-team-xecuter-custody
https://medium.com/swlh/watch-paint-dry-how-i-got-a-game-on-the-steam-store-without-anyone-from-valve-ever-looking-at-it-2e476858c753#.z05q2nykc
https://www.lemonde.fr/police-justice/article/2022/05/27/voler-des-societes-qui-font-des-milliards-qu-est-ce-que-j-en-ai-a-faire-max-louarn-c-ur-de-hackeur_6127821_1653578.html
https://www.theverge.com/2020/11/20/21579392/nintendo-big-house-super-smash-bros-melee-tournament-slippi-cease-desist
https://www.youtube.com/watch?v=U7VwtOrwceo
https://www.youtube.com/watch?v=5sNIE5anpik
Omar Avilez worked in the CSIRT of the Dominican Republic when a major cyber security incident erupted. Omar walks us through what happened and the incident response procedures that he went through.
Breakmaster Cylinder’s new album: https://breakmastercylinder.bandcamp.com/album/the-moon-all-that.
Sponsors
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Flare. Flare automates monitoring across the dark & clear web to detect high-risk exposure, before threat actors have a chance to leverage it. Their unified solution makes it easy to rapidly identify risks across thousands of sources, including developers leaking secrets on public GitHub Repositories, threat actors selling infected devices on dark web markets, and targeted attacks being planned on illicit Telegram Channels. Visit https://flare.io to learn more.
Sources
https://www.wired.com/story/costa-rica-ransomware-conti/
https://malpedia.caad.fkie.fraunhofer.de/details/win.bandook
https://www.youtube.com/watch?v=QHYH0U66K5Q
https://www.youtube.com/live/prCr7Z94078
https://www.eff.org/deeplinks/2023/02/uncle-sow-dark-caracal-latin-america
https://www.bleepingcomputer.com/news/security/quantum-ransomware-attack-disrupts-govt-agency-in-dominican-republic/
https://www.welivesecurity.com/2021/07/07/bandidos-at-large-spying-campaign-latin-america/
Attribution
Darknet Diaries is created by Jack Rhysider.
Assembled by Tristan Ledger.
Episode artwork by odibagas.
Mixing by Proximity Sound.
Theme music created by Breakmaster Cylinder. Theme song available for listen and download at bandcamp. Or listen to it on Spotify.
Deviant Ollam is a physical penetration specialist. That means he’s paid to break into buildings to see if the building is secure or not. He has done this for a long time and has a lot of tricks up his sleeve to get into buildings. In this episode we hear 3 stories of him breaking into buildings for a living.
You can find more about Deviant on the following sites:
https://twitter.com/deviantollam
https://www.instagram.com/deviantollam
https://youtube.com/deviantollam
https://defcon.social/@deviantollam
https://deviating.net/
Sponsors
Support for this show comes from ThreatLocker. ThreatLocker has built-in endpoint security solutions that strengthen your infrastructure from the ground up with a zero trust posture. ThreatLocker’s Allowlisting gives you a more secure approach to blocking exploits of known and unknown vulnerabilities. ThreatLocker provides zero trust control at the kernel level. Learn more at www.threatlocker.com.
This show is sponsored by Packetlabs. They’ve created the Penetration Testing Buyer’s guide - a comprehensive resource that will help you plan, scope, and execute your Penetration Testing projects. Inside, you’ll find valuable information on frameworks, standards, methodologies, cost factors, reporting options, and what to look for in a provider. https://guide.packetlabs.net/.
Support for this show comes from Drata. Drata streamlines your SOC 2, ISO 27001, PCI DSS, HIPAA, GDPR & many other compliance frameworks, and provides 24-hour continuous control monitoring so you focus on scaling securely. Listeners of Darknet Diaries can get 10% off Drata and waived implementation fees at drata.com/darknetdiaries.
One day Connor Tumbleson got an email saying his identity has been stolen. And this was one of the strangest days he’s ever had.
Sponsors
Support for this show comes from Quorum Cyber. Their mantra is: “We help good people win.” If you’re looking for a partner to help you reduce risk and defend against the threats that are targeting your business — and especially if you are interested in Microsoft Security — reach out to Qurotum Cyber at quorumcyber.com.
Skiff is a collaboration platform built for privacy from the ground up. Every document, note, and idea you write is end-to-end encrypted and completely private. Only you and your trusted collaborators can see what you’ve created. Try it out at https://skiff.com.
Support for this show comes from AttackIQ. AttackIQ’s security optimization platform emulates the adversary with realism to test your security program, generating real-time performance data to improve your security posture. They also offer free training. Head to attackiq.com to get a closer look at how AttackIQ can help you today.
Sources
https://connortumbleson.com/
https://krebsonsecurity.com/2022/10/glut-of-fake-linkedin-profiles-pits-hr-against-the-bots/
Snippet from Darknet Diaries ep 119 about North Korean’s getting tech jobs to steal bitcoin https://www.youtube.com/watch?v=v1ik6bAwELA
Attribution
Assembled by Tristan Ledger.
Sound design by Garrett Tiedemann.
Episode artwork by odibagas.
Mixing by Proximity Sound.
Theme music created by Breakmaster Cylinder.
Sam Bent, a.k.a. DoingFedTime, brings us a story of what it was like being a darknet market vendor.
Learn more about Sam at https://www.doingfedtime.com/.
Sponsors
Support for this show comes from Akamai Connected Cloud (formerly Linode). Akamai Connected Cloud supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Support for this show comes from Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Andy Greenberg (https://twitter.com/a_greenberg) brings us a gut wrenching story of how criminal investigators used bitcoin tracing techniques to try to find out who was at the center of a child sexual abuse darkweb website.
This story is part of Andy’s new book “Tracers in the Dark: The Global Hunt for the Crime Lords of Cryptocurrency”. An affiliate link to the book on Amazon is here: https://amzn.to/3VkjSh7.
Sponsors
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Join us as we sit down with Jason Haddix (https://twitter.com/Jhaddix), a renowned penetration tester who has made a name for himself by uncovering vulnerabilities in some of the world’s biggest companies. In this episode, Jason shares his funny and enlightening stories about breaking into buildings and computers, and talks about the time he discovered a major security flaw in a popular mobile banking app.
Sponsors
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Support for this show comes from Arctic Wolf. Arctic Wolf is the industry leader in security operations solutions, delivering 24x7 monitoring, assessment, and response through our patented Concierge Security model. They work with your existing tools and become an extension of your existing IT team. Visit arcticwolf.com/darknet to learn more.
Brett Johnson, AKA Gollumfun (twitter.com/GOllumfun) was involved with the websites Counterfeit Library and Shadow Crew. He tells his story of what happened there and some of the crimes he committed.
In part 2, his past catches up to him.
Listen to more of Brett on his own show. https://www.thebrettjohnsonshow.com/.
Brett Johnson, AKA Gollumfun (twitter.com/GOllumfun) was involved with the websites Counterfeit Library and Shadow Crew. He tells his story of what happened there and some of the crimes he committed.
Sponsors
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Maddie Stone is a security researcher for Google’s Project Zero. In this episode we hear what it’s like battling zero day vulnerabilities.
Sponsors
Support for this show comes from Zscalar. Zscalar zero trust exchange will scrutinize the traffic and permit or deny traffic based on a set of rules. This is so much more secure than letting data flow freely internally. And it really does mitigate ransomware outbreaks. The Zscaler Zero Trust Exchange gives YOU confidence in your security to feel empowered to focus on other parts of your business, like digital transformation, growth, and innovation. Check out the product at zscaler.com.
Support for this show comes from Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Sources
https://www.sophos.com/en-us/medialibrary/pdfs/technical%20papers/yu-vb2013.pdf
https://www.youtube.com/watch?v=s0Tqi7fuOSU
https://www.vice.com/en/article/4x3n9b/sometimes-a-typo-means-you-need-to-blow-up-your-spacecraft
REvil is the name of a ransomware service as well as a group of criminals inflicting ransomware onto the world. Hear how this ransomware shook the world.
A special thanks to our guest Will, a CTI researcher with Equinix.
Sponsors
Support for this show comes from Zscalar. Zscalar zero trust exchange will scrutinize the traffic and permit or deny traffic based on a set of rules. This is so much more secure than letting data flow freely internally. And it really does mitigate ransomware outbreaks. The Zscaler Zero Trust Exchange gives YOU confidence in your security to feel empowered to focus on other parts of your business, like digital transformation, growth, and innovation. Check out the product at zscaler.com.
Support for this show comes from Arctic Wolf. Arctic Wolf is the industry leader in security operations solutions, delivering 24x7 monitoring, assessment, and response through our patented Concierge Security model. They work with your existing tools and become an extension of your existing IT team. Visit arcticwolf.com/darknet to learn more.
Jeremiah Roe is a seasoned penetration tester. In this episode he tells us about a time when he had to break into a building to prove it wasn’t as secure as the company thought.
You can catch more of Jeremiah on the We’re In podcast.
Sponsors
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Snyk. Snyk is a developer security platform that helps you secure your applications from the start. It automatically scans your code, dependencies, containers, and cloud infrastructure configs — finding and fixing vulnerabilities in real time. Create your free account at snyk.co/darknet.
What do you get when you combine social engineering, email, crime, finance, and the money stream flowing through big tech? Evaldas Rimašauskas comes to mind. He combined all these to make his big move. A whale of a move.
Sponsors
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Support for this show comes from Axonius. The Axonius solution correlates asset data from your existing IT and security solutions to provide an always up-to-date inventory of all devices, users, cloud instances, and SaaS apps, so you can easily identify coverage gaps and automate response actions. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Investing in the stock market can be very profitable. Especially if you can see into the future. This is a story of how a group of traders and hackers got together to figure out a way to see into the future and make a lot of money from that.
Sponsors
Support for this show comes from Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this show comes from Juniper Networks. Juniper Networks is dedicated to simplifying network operations and driving superior experiences for end users. Visit juniper.net/darknet to learn more about how Juniper’s Zero Trust Data Center provides uncompromising visibility across all your data center environments. Visit juniper.net/darknet to learn more.
In this episode we hear some insider threat stories from Lisa Forte.
Sponsors
Support for this show comes from Axonius. Securing assets — whether managed, unmanaged, ephemeral, or in the cloud — is a tricky task. The Axonius Cybersecurity Asset Management Platform correlates asset data from existing solutions to provide an always up-to-date inventory, uncover gaps, and automate action. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Support for this show comes from Snyk. Snyk is a developer security platform that helps you secure your applications from the start. It automatically scans your code, dependencies, containers, and cloud infrastructure configs — finding and fixing vulnerabilities in real time. Create your free account at snyk.co/darknet.
Attribution
Darknet Diaries is created by Jack Rhysider.
Editing by Damienne. Assembled by Tristan Ledger. Sound designed by Andrew Meriwether.
Episode artwork by odibagas.
Mixing by Proximity Sound.
Theme music created by Breakmaster Cylinder. Theme song available for listen and download at bandcamp. Or listen to it on Spotify.
In this episode we hear some penetration test stories from Ed Skoudis (twitter.com/edskoudis). We also catch up with Beau Woods (twitter.com/beauwoods) from I am The Cavalry (iamthecavalry.org).
Sponsors
Support for this show comes from Axonius. Securing assets — whether managed, unmanaged, ephemeral, or in the cloud — is a tricky task. The Axonius Cybersecurity Asset Management Platform correlates asset data from existing solutions to provide an always up-to-date inventory, uncover gaps, and automate action. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Zscalar. Zscalar zero trust exchange will scrutinize the traffic and permit or deny traffic based on a set of rules. This is so much more secure than letting data flow freely internally. And it really does mitigate ransomware outbreaks. The Zscaler Zero Trust Exchange gives YOU confidence in your security to feel empowered to focus on other parts of your business, like digital transformation, growth, and innovation. Check out the product at zscaler.com/darknet.
Support for this podcast comes from Cybereason. Cybereason reverses the attacker’s advantage and puts the power back in the defender’s hands. End cyber attacks. From endpoints to everywhere. Learn more at Cybereason.com/darknet.
View all active sponsors.
Attribution
Darknet Diaries is created by Jack Rhysider.
Editing by Damienne. Assembled by Tristan Ledger. Sound designed by Andrew Meriwether.
Episode artwork by odibagas.
Audio cleanup by Proximity Sound.
Theme music created by Breakmaster Cylinder.
This is the story about when Mohammed Aldoub, AKA Voulnet, (twitter.com/Voulnet) found a vulnerability on Virus Total and Tweeted about it.
Sponsors
Support for this podcast comes from Cybereason. Cybereason reverses the attacker’s advantage and puts the power back in the defender’s hands. End cyber attacks. From endpoints to everywhere. Learn more at Cybereason.com/darknet.
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
Sources
https://www.cyberscoop.com/story/trial-error-kuwait-mohammed-aldoub-case/
In this episode we interview journalist Geoff White to discuss some of the recent crypto currency heists that have been happening. Geoff has been tracking a certain group of thieves for some time and shares his knowledge of what he’s found.
Much of what we talk about in this episode has been published in Geoff’s new book The Lazarus Heist: From Hollywood to High Finance: Inside North Korea’s Global Cyber War (https://amzn.to/3mKf1qB).
Sponsors
Support for this show comes from Axonius. Securing assets — whether managed, unmanaged, ephemeral, or in the cloud — is a tricky task. The Axonius Cybersecurity Asset Management Platform correlates asset data from existing solutions to provide an always up-to-date inventory, uncover gaps, and automate action. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. axonius.com/darknet
Support for this show comes from Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
This is the story of Joseph Harris (https://twitter.com/akad0c). When he was a young teen he got involved with stealing video game accounts and selling them for money. This set him on a course where he flew higher and higher until he got burned.
Joseph sometimes demonstrates vulnerabilities he finds on his YouTube channel https://www.youtube.com/channel/UCdcuF5Zx6BiYmwnS-CiRAng.
Listen to episode 112 “Dirty Coms” to hear more about what goes on in the communities Joseph was involed with.
Sponsors
Support for this show comes from Axonius. Securing assets — whether managed, unmanaged, ephemeral, or in the cloud — is a tricky task. The Axonius Cybersecurity Asset Management Platform correlates asset data from existing solutions to provide an always up-to-date inventory, uncover gaps, and automate action. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks.
Support for this show comes from Synack. Synack is a penetration testing firm. But they also have a community of, people like you, who earn regular money by legally hacking. If you’re interested in getting paid to hack, visit them now at synack.com/red-team, and click ‘apply now.’
Daniel Kelley (https://twitter.com/danielmakelley) was equal parts mischievousness and clever when it came to computers. Until the day his mischief overtook his cleverness.
Sponsors
Support for this show comes from Keeper Security. Keeper Security’s is an enterprise password management system. Keeper locks down logins, payment cards, confidential documents, API keys, and database passwords in a patented Zero-Knowledge encrypted vault. And, it takes less than an hour to deploy across your organization. Get started by visiting keepersecurity.com/darknet.
Support for this podcast comes from Cybereason. Cybereason reverses the attacker’s advantage and puts the power back in the defender’s hands. End cyber attacks. From endpoints to everywhere. Learn more at Cybereason.com/darknet.
Jim Lawler, aka “Mad Dog”, was a CIA case officer for 25 years. In this episode we hear some of the stories he has and things he did while working in the CIA.
Jim has two books out. Affiliate links below.
Living Lies: A Novel of the Iranian Nuclear Weapons Program https://amzn.to/3s0Ppca
In the Twinkling of an Eye: A Novel of Biological Terror and Espionage https://amzn.to/3y7B4OL
Sponsors
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Support for this show comes from Juniper Networks. Juniper Networks is dedicated to simplifying network operations and driving superior experiences for end users. Visit juniper.net/darknet to learn more about how Juniper’s Zero Trust Data Center provides uncompromising visibility across all your data center environments. Visit juniper.net/darknet to learn more.
Some video game players buy cheats to win. Let’s take a look at this game cheating industry to see who the players are.
Sponsors
Support for this show comes from Axonius. Securing assets — whether managed, unmanaged, ephemeral, or in the cloud — is a tricky task. The Axonius Cybersecurity Asset Management Platform correlates asset data from existing solutions to provide an always up-to-date inventory, uncover gaps, and automate action. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this podcast comes from Cybereason. Cybereason reverses the attacker’s advantage and puts the power back in the defender’s hands. End cyber attacks. From endpoints to everywhere. Learn more at Cybereason.com/darknet.
HD Moore (https://twitter.com/hdmoore) invented a hacking tool called Metasploit. He crammed it with tons of exploits and payloads that can be used to hack into computers. What could possibly go wrong? Learn more about what HD does today by visiting rumble.run/.
Sponsors
Support for this show comes from Quorum Cyber. They exist to defend organisations against cyber security breaches and attacks. That’s it. No noise. No hard sell. If you’re looking for a partner to help you reduce risk and defend against the threats that are targeting your business — and specially if you are interested in Microsoft Security - reach out to www.quorumcyber.com.
Support for this show comes from Snyk. Snyk is a developer security platform that helps you secure your applications from the start. It automatically scans your code, dependencies, containers, and cloud infrastructure configs — finding and fixing vulnerabilities in real time. And Snyk does it all right from the existing tools and workflows you already use. IDEs, CLI, repos, pipelines, Docker Hub, and more — so your work isn’t interrupted. Create your free account at snyk.co/darknet.
Adam got a job doing IT work at a learning academy. He liked it and was happy there and feeling part of the team. But a strange series of events took him in another direction, that definitely didn’t make him happy.
Sponsors
Support for this show comes from Axonius. Securing assets — whether managed, unmanaged, ephemeral, or in the cloud — is a tricky task. The Axonius Cybersecurity Asset Management Platform correlates asset data from existing solutions to provide an always up-to-date inventory, uncover gaps, and automate action. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this podcast comes from Cybereason. Cybereason reverses the attacker’s advantage and puts the power back in the defender’s hands. End cyber attacks. From endpoints to everywhere. Learn more at Cybereason.com/darknet.
Support for this show comes from Varonis. Do you wonder what your company’s ransomware blast radius is? Varonis does a free cyber resilience assessment that tells you how many important files a compromised user could steal, whether anything would beep if they did, and a whole lot more. They actually do all the work – show you where your data is too open, if anyone is using it, and what you can lock down before attackers get inside. They also can detect behavior that looks like ransomware and stop it automatically. To learn more visit www.varonis.com/darknet.
This episode we talk with a guy named “Drew” who gives us a rare peek into what some of the young hackers are up to today. From listening to Drew, we can see that times are changing for the motive behind hacking. In the ’90s and ’00s it was done for fun and curiosity. In the ’10s Anonymous showed us what Hacktivism is. And now, in the ’20s, the young hackers seem to be profit driven.
Sponsors
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Support for this show comes from Juniper Networks. Juniper Networks is dedicated to simplifying network operations and driving superior experiences for end users. Visit juniper.net/darknet to learn more about how Juniper Secure Edge can help you keep your remote workforce seamlessly secure wherever they are.
ZeuS is a banking trojan. Designed to steal money from online bank user’s accounts. This trojan became so big, that it resulted in one of the biggest FBI operations ever.
Sponsors
Support for this show comes from Axonius. Securing assets — whether managed, unmanaged, ephemeral, or in the cloud — is a tricky task. The Axonius Cybersecurity Asset Management Platform correlates asset data from existing solutions to provide an always up-to-date inventory, uncover gaps, and automate action. Axonius gives IT and security teams the confidence to control complexity by mitigating threats, navigating risk, decreasing incidents, and informing business-level strategy — all while eliminating manual, repetitive tasks. Visit axonius.com/darknet to learn more and try it free.
Support for this show comes from Keeper Security. Keeper Security’s is an enterprise password management system. Keeper locks down logins, payment cards, confidential documents, API keys, and database passwords in a patented Zero-Knowledge encrypted vault. And, it takes less than an hour to deploy across your organization. Get started by visiting keepersecurity.com/darknet.
This episode tells the stories of some of the worlds biggest spamming botnets. We’ll talk about the botnets Rustock, Waledac, and Cutwail. We’ll discover who was behind them, what their objectives were, and what their fate was.
Sponsors
Support for this show comes from Juniper Networks (hyperlink: juniper.net/darknet). Juniper Networks is dedicated to simplifying network operations and driving superior experiences for end users. Visit juniper.net/darknet to learn more about how Juniper Secure Edge can help you keep your remote workforce seamlessly secure wherever they are.
Support for this podcast comes from Cybereason. Cybereason reverses the attacker’s advantage and puts the power back in the defender’s hands. End cyber attacks. From endpoints to everywhere. Learn more at Cybereason.com/darknet.
TeaMp0isoN was a hacking group that was founded by TriCk and MLT (twitter.com/0dayWizard). They were responsible for some high profile hacks. But in this story it’s not the rise that’s most interesting. It’s the fall.
Sponsors
Support for this show comes from Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this podcast comes from Cybereason. Cybereason reverses the attacker’s advantage and puts the power back in the defender’s hands. End cyber attacks. From endpoints to everywhere. Learn more at Cybereason.com/darknet.
This is the story of Marq (twitter.com/dev_null321). Which involves passwords, the dark web, and police.
Sponsors
Support for this podcast comes from Cybereason. Cybereason reverses the attacker’s advantage and puts the power back in the defender’s hands. End cyber attacks. From endpoints to everywhere. Learn more at Cybereason.com/darknet.
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
View all active sponsors.
Sources
Court records and news articles were used to fact check this episode. However Marq requested that links to his full name not be made available.
https://techcrunch.com/2019/12/19/ring-doorbell-passwords-exposed/
https://www.wired.com/2010/03/hacker-bricks-cars/
Alethe is a social engineer. Professionally she tries to trick people to give her passwords and access that she shouldn’t have. But her journey to this point is interesting and in this episode she tells us how she became a social engineer.
Follow Alethe on Twitter: https://twitter.com/AletheDenis
Sponsors
Support for this show comes from Skiff. Skiff is a collaboration platform built for privacy from the ground up. Every document, note, and idea you write is end-to-end encrypted and completely private. Only you and your trusted collaborators can see what you’ve created. Try it out at https://www.skiff.org/darknet.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
How much online abuse are you willing to take before you decide to let your abuser have what they want? Unfortunately, this is a decision that many people have to ask themselves. If someone can threaten you physically, it bypasses whatever digital security you have in place.
Thanks to https://twitter.com/jw for sharing this harrowing story with us.
Affiliate links to books:
The Smart Girl’s Guide to Privacy: https://www.amazon.com/gp/product/1593276486/ref=as_li_tl?ie=UTF8&camp=1789&creative=9325&creativeASIN=1593276486&linkCode=as2&tag=tunn01-20&linkId=0a8ee2ca846534f77626757288d77e00
Extreme Privacy:https://www.amazon.com/gp/product/B0898YGR58/ref=as_li_tl?ie=UTF8&camp=1789&creative=9325&creativeASIN=B0898YGR58&linkCode=as2&tag=tunn01-20&linkId=575c5ed0326484f0b612f000621b407f
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET.
Support for this show comes from Ping Identity, champions of identity for the global enterprise. Give your users a loveable login solution. Visit www.pingidentity.com/.
View all active sponsors.
Joseph Cox (https://twitter.com/josephfcox), Senior Staff Writer at Motherboard (https://www.vice.com/en/topic/motherboard), joins us to talk about the world of encrypted phones.
Books
Affiliate links to books:
The Smart Girl’s Guide to Privacy: https://www.amazon.com/gp/product/1593276486/ref=as_li_tl?ie=UTF8&camp=1789&creative=9325&creativeASIN=1593276486&linkCode=as2&tag=tunn01-20&linkId=0a8ee2ca846534f77626757288d77e00
Extreme Privacy:https://www.amazon.com/gp/product/B0898YGR58/ref=as_li_tl?ie=UTF8&camp=1789&creative=9325&creativeASIN=B0898YGR58&linkCode=as2&tag=tunn01-20&linkId=575c5ed0326484f0b612f000621b407f
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET.
Support for this show comes from Ping Identity, champions of identity for the global enterprise. Give your users a loveable login solution. Visit www.pingidentity.com/.
View all active sponsors.
Arya Ebrahami has had quite a personal relationship with darknet marketplaces. In this episode you’ll hear about his adventures on tor. Arya’s current project is https://lofi-defi.com.
Sponsors
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
View all active sponsors.
Sources
https://www.nbcwashington.com/news/local/27-arrested-in-prince-william-county-narcotics-investigation/58441/
https://patch.com/virginia/manassas/undercover-narcotics-operation-nets-27-arrrests-xanax-distribution-ring
Fabio Viggiani is an incident responder. In this episode he talks about the story when one of his clients were breached.
Sponsors
Support for this show, and for stretched security teams, comes from SOC.OS. Too many security alerts means alert fatigue for under-resourced SecOps teams. Traditional tools aren’t solving the problem. SOC.OS is the lightweight, cost-effective, and low-maintenance solution for your team. Centralise, enrich, and correlate your security alerts into manageable, prioritised clusters. Get started with an extended 3-month free trial at https://socos.io/darknet.
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET.
Sources
https://www.reuters.com/investigates/special-report/china-cyber-cloudhopper
https://www.reuters.com/article/us-china-cyber-cloudhopper-companies-exc-idUSKCN1TR1D4
https://www.fbi.gov/wanted/cyber/apt-10-group
https://www.youtube.com/watch?v=277A09ON7mY
https://www.wsj.com/articles/ghosts-in-the-clouds-inside-chinas-major-corporate-hack-11577729061
https://www.technologyreview.com/2018/12/20/239760/chinese-hackers-allegedly-stole-data-of-more-than-100000-us-navy-personnel/
Frank Bourassa had an idea. He was going to make money. Literally. Listen to the story of a master counterfeiter.
In 2014 the Puerto Rico Lottery was mysteriously losing money. Listen to this never before told story about what happened and who did it.
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET.
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Sources
https://en.wikipedia.org/wiki/Puerto_Rico_Lottery
https://www.justice.gov/usao-pr/pr/10-individuals-indicted-drug-trafficking-and-money-laundering
https://www.dea.gov/press-releases/2014/07/22/caribbean-corridor-strike-force-arrests-10-individuals-indicted-drug
https://casetext.com/case/united-states-v-delfin-robles-alvarez-7
The NSO Group creates a spyware called Pegasus which gives someone access to the data on a mobile phone. They sell this spyware to government agencies around the world. How is it used and what kind of company is the NSO Group?
Thanks to John Scott-Railton and Citizen Lab for investigating this and sharing their research.
Sponsors
Support for this show comes from Detectify. Try their web vulnerability scanner free. Go to https://detectify.com/?utm_source=podcast&utm_medium=referral&utm_campaign=DARKNET
Support for this show comes from Ping Identity, champions of identity for the global enterprise. Give your users a loveable login solution. Visit www.pingidentity.com/.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
For a full list of sources used in this episode and complete transcripts visit https://darknetdiaries.com.
Igor works as a private investigator in NYC. He’s often sitting in cars keeping a distant eye on someone with binoculars. Or following someone through the busy streets of New York. In this episode we hear about a time when Igor was on a case but sensed that something wasn’t right.
Sponsors
Support for this show comes from Exabeam. Exabeam lets security teams see what traditional tools can’t, with automated threat detection and triage, complete visibility across the entire IT environment and advanced behavioral analytics that distinguishes real threats from perceived ones, so security teams stay ahead and businesses keep moving — without fear of the unknown. When the security odds are stacked against you, outsmart them from the start with Exabeam. Learn more at https://exabeam.com/DD.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
View all active sponsors.
Sources
Article: The Case of the Bumbling Spy
Podcast: The Catch and Kill Podcast with Ronan Farrow
Zero day brokers are people who make or sell malware that’s sold to people who will use that malware to exploit people. It’s a strange and mysterious world that not many people know a lot about. Nicole Perlroth, who is a cybersecurity reporter for the NY Times, dove in head first which resulted in her writing a whole book on it.
Affiliate link for book: This is How They Tell Me The World Ends (https://www.amazon.com/gp/product/1635576059/ref=as_li_tl?ie=UTF8&camp=1789&creative=9325&creativeASIN=1635576059&linkCode=as2&tag=tunn01-20&linkId=0aa8c966d98b49a7927bfc29aac76bbe)
Audiobook deal: Try Audible Premium Plus and Get Up to Two Free Audiobooks (https://www.amazon.com/Audible-Free-Trial-Digital-Membership/dp/B00NB86OYE/?ref_=assoc_tag_ph_1485906643682&_encoding=UTF8&camp=1789&creative=9325&linkCode=pf4&tag=tunn01-20&linkId=31042b955d5e6d639488dc084711d033)
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET.
Support for this show comes from Privacy.com. Privacy allows you to create anonymous debit cards instantly to use for online shopping. Visit privacy.com/darknet to get a special offer.
Sources
What if someone wanted to own your Instagram account? Not just control it, but make it totally theirs. This episode tells the story of how someone tried to steal an Instagram account from someone.
Sponsors
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Sources
Nicole Beckwith wears a lot of hats. She’s a programmer, incident responder, but also a cop and a task force officer with the Secret Service. In this episode she tells a story which involves all of these roles.
https://twitter.com/NicoleBeckwith
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET.
Support for this show comes from Exabeam. Exabeam lets security teams see what traditional tools can’t, with automated threat detection and triage, complete visibility across the entire IT environment and advanced behavioral analytics that distinguishes real threats from perceived ones, so security teams stay ahead and businesses keep moving — without fear of the unknown. When the security odds are stacked against you, outsmart them from the start with Exabeam. Learn more at https://exabeam.com/DD.
Sources
Jon and Brian are penetration testers who both worked at a place called RedTeam Security. They’re paid to break into buildings and hack into networks to test the security of those buildings. In this episode they bring us a story of how they prepare and execute a mission like this. But even with all the preparation, something still goes terribly wrong.
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET.
Support for this show comes from Ping Identity, champions of identity for the global enterprise. Give your users a loveable login solution. Visit www.pingidentity.com/.
Sources
Chris Davis has been stopping IT security threats for decades. He’s currently running the company Hyas that he started. In this episode he tells a few tales of some threats that he helped stop.
Sponsors
Support for this show comes from Exabeam. Exabeam lets security teams see what traditional tools can’t, with automated threat detection and triage, complete visibility across the entire IT environment and advanced behavioral analytics that distinguishes real threats from perceived ones, so security teams stay ahead and businesses keep moving — without fear of the unknown. Learn more by visiting exabeam.com/dd.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Sources
Kik is a wildly popular chat app. Their website says that 1 in 3 American teenagers use Kik. But something dark is brewing on Kik.
The Pirate Bay is a website, a search engine, which has an index of torrent files. A lot of copyrighted material is listed on the site, but the site doesn’t store any of the copyrighted material. It just points the user to where you can download it from. So for a while The Pirate Bay has been the largest places you can find pirated movies, music, games, and apps. But this site first came up 2003. And is still up and operation now, 18 years later! You would think someone would shut this place down by now. How does the biggest source for copyrighted material stay up and online for that long? Listen to this episode to find out.
Sponsors
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
What happens when an unauthorized intruder gets into the network of a major bank? Amélie Koran aka webjedi was there for one of these intrusions and tells us the story of what happened.
You can find more talks from Amélie at her website webjedi.net.
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
This podcast is sponsored by Navisite. Accelerate IT transformation to respond to new demands, lower costs and prepare for whatever comes next. Visit Navisite.com/go.
Sources
Meet Jenny Radcliffe, the People Hacker. She’s a social engineer and physical penetration tester. Which means she gets paid to break into buildings and test their security. In this episode she tells us a few stories of some penetration testing jobs she’s done.
Sponsors
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
This podcast is sponsored by Navisite. Accelerate IT transformation to respond to new demands, lower costs and prepare for whatever comes next. Visit Navisite.com/go.
Sources
The threat research team at Cybereason uncovered an interesting piece of malware. Studied it and tracked it. Which lead them to believe they were dealing with a threat actor known as Molerats.
Sponsors
This episode is sponsored by Cybereason. Cybereason reverses the attacker’s advantage and puts the power back in your hands. Their future-ready attack platform gives defenders the wisdom to uncover, understand, and piece together multiple threats. And the precision focus to end cyberattacks instantly – on computers, mobile devices, servers, and the cloud. They do all this through a variety of tools they’ve developed such as antivirus software, endpoint monitoring, and mobile threat detection tools. They can give you the power to do it yourself, or they can do all the monitoring and respond to threats in your environment for you. Or you can call them after an incident to get help cleaning up. If you want to monitor your network for threats, check out what Cybereason can do for you. Cybereason. End cyber attacks. From endpoints to everywhere. Learn more at Cybereason.com/darknet.
Sources
Victor looks for vulnerabilities on the web and reports them responsibly. This is the story about discloser number 5780.
Listen to episodes 86, and 87 before this one to be caught up on the story leading up to this.
Sponsors
This podcast is sponsored by Navisite. Accelerate IT transformation to respond to new demands, lower costs and prepare for whatever comes next. Visit Navisite.com/go.
This podcast is sponsored by the JSCM Group. They have a service called ClosedPort: Scan, and it’s is a monthly Penetration Test performed by Cyber Security Experts. Contact JSCM Group today at jscmgroup.com/darknet.
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
In 2016 the LinkedIn breach data became available to the public. What the Guild of the Grumpy Old Hackers did with it then is quite the story. Listen to Victor, Edwin, and Mattijs tell their story.
Sponsors
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Support for this show comes from Privacy.com. Privacy allows you to create anonymous debit cards instantly to use for online shopping. Visit privacy.com/darknet to get a special offer.
In 2012, LinkedIn was the target of a data breach. A hacker got in and stole millions of user details. Username and password hashes were then sold to people willing to buy. This episode goes over the story of what happened.
For a good password manager, check out LastPass.
Sponsors
Support for this episode comes from Quadrant Information Security. If you need a team of around the clock analysts to monitor for threat in your network using a custom SIEM, check out what Quadrant can do for you by visiting www.quadrantsec.com.
Support for this show comes from Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
This is the story of Cam Harrison, aka “kilobit” and his rise and fall as a prominent carder.
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this episode comes from Oracle for Startups. Oracle for Startups delivers enterprise cloud at a startup price tag, with free cloud credits and 70% off industry-leading cloud services to help you reel in the big fish—confidently. To learn more, visit Oracle.com/goto/darknet.
Sources
How bad is it if you post your boarding pass on Instagram? Our guest, “Alex” decides to figure this out for themself and has quite a story about what happened. You can read more from “Alex” on their blog https://mango.pdf.zone.
We also hear from TProphet who’s here to give us some travel hacks to save tons on airfare when we start traveling again. You can learn more about TProphet’s travel hacks at https://seat31b.com or https://award.cat.
Sponsors
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Support for this show comes from Tanium. With Tanium you can gain real-time security and operational data directly from your endpoints – along with the ability to take action on, and create reports from, that data – in just minutes, so that you and your teams can have the insight and capability necessary to accomplish the mission effectively. Learn more at https://federal.tanium.com.
Sources
In this episode we interview two NSA Cryptologists, Marcus J. Carey and Jeff Man. We hear their story of how they got into the NSA and what they did while there.
To hear more stories from Jeff tune into Paul’s Security Weekly where Jeff is a regular co-host and shares a lot of stories and insights.
Marcus has written several books on security. They are Tribe of Hackers, Tribe of Hackers Blue Team, Tribe of Hackers Red Team, Tribe of Hackers Security Leaders, Think in Code, and a childrens book called Three Little Hackers.
Also check out the Tribe of Hackers podcast to hear interviews with all these amazing people!
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
The Zero Day Initiative runs a hacker contest called Pwn2Own. The contest calls the best hackers in the world to demonstrate they can hack into software that should be secure. Like browsers, phones, and even cars. A lot of vulnerabilities are discovered from this event which means vendors must fix them. Whoever can demonstrate the most vulnerabilities will be crowned the “Master of Pwn”.
Thanks to Dustin Childs and Brian Gorenc from ZDI to hear all about Pwn2Own.
Thanks to Radek and Pedro for sharing their experiences of becoming the Masters of Pwn.
Sponsors
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Support for this show comes from Kars 4 Kids. Donate your car today, this organization will sell to use for their charity.
Sources
This is the story of a darknet marketplace vendor we’ll name V. V tells his story of how he first became a buyer, then transitioned into seller.
This episode talks about drugs. Listener discretion is advised.
If you want to contact V his email is at https://darknetdiaries.com/episode/81.
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
In this episode we hear a story from a social engineer who’s job it is to get people to do things they don’t want to do. Why? For profit.
Sponsors
Support for this episode comes from SentinelOne which can protect and assistwith ransomeware attacks. On top of that, SentinelOne offers threat hunting, visibility, and remote administration tools to manage and protect any IoT devices connected to your network. Go to SentinelOne.com/DarknetDiaries for your free demo. Your cybersecurity future starts today with SentinelOne.
Support for this show comes from Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
What do you do when you find yourself the target of a massive hacking campaign, and you are getting thousands of phishing emails and someone following you in your car. You might turn to Citizen Lab who has the ability to research who is behind this and help bring the hackers to justice.
Our guests this episodes are Adam Hulcoop and John Scott-Railton of Citizen Lab. This episode also has an interview with Matthew Earl of Shadowfall.
Sponsors
Support for this show comes from LastPass by LogMeIn. LastPass is a great password manager but it can do so much more. It can setup 2FA for your company, or use it to monitor what your users are doing in the network. Visit LastPass.com/Darknet to start your 14 day free trial.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Nerdcore music is music for nerds. In this episode we hear from some of the musicians who make Nerdcore music.
This episode features guests ytcracker, Ohm-I, and Dual Core.
Content warning: This episode has explicit lyrics.
Music
For a playlist of music used in this episode visit darknetdiaries.com/episode/78.
Sponsors
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
In February 2018, during the Winter Olympics in Pyeongchang South Korea, a cyber attack struck, wiping out a lot of the Olympic’s digital infrastructure. Teams rushed to get things back up, but it was bad. Malware had repeatedly wiped the domain controllers rendering a lot of the network unusable. Who would do such a thing?
We will talk with Andy Greenberg to discuss Olympic Destroyer, a chapter from his book Sandworm (affiliate link).
Sponsors
Support for this show comes from Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and get a special offer.
Support for this show comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
This is the story about how someone hacked into JP Morgan Chase, one of the biggest financial institutions in the world. It’s obvious why someone would want to break into a bank right? Well the people who hacked into this bank, did not do it for obvious reasons. The hackers are best described as knaves. Which are tricky, deceitful fellows.
Sponsors
Support for this show comes from LastPass by LogMeIn. LastPass is a great password manager but it can do so much more. It can setup 2FA for your company, or use it to monitor what your users are doing in the network. Visit LastPass.com/Darknet to start your 14 day free trial.
Support for this episode comes from SentinelOne which can protect and assistwith ransomeware attacks. On top of that, SentinelOne offers threat hunting, visibility, and remote administration tools to manage and protect any IoT devices connected to your network. Go to SentinelOne.com/DarknetDiaries for your free demo. Your cybersecurity future starts today with SentinelOne.
Support for this show comes from IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
For a complete list of sources and a full transcript of the show visit darknetdiaries.com/episode/76.
From 2009 to 2013 the communication channels the CIA uses to contact assets in foreign countries was compromised. This had terrifying consequences.
Guests this episodes are Jenna McLaughlin and Zach Dorfman.
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
This episode was sponsored by Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Sources
Attribution
Darknet Diaries is created by Jack Rhysider.
Research assistance this episode from Yael Grauer.
Poker is a competitive game. Unlike other casino games, poker is player vs player. Criminal hackers have understood this for a while and sometimes hack the other players to get an edge. And that small edge can result in millions of dollars in winnings.
This episode contains a story from Mikko Hypponen of F-Secure. We also interview Mikko to know more about him and the history of malware.
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
This episode was sponsored by Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Sources
It is recommend to listen to episodes 53 “Shadow Brokers”, 71 “FDFF”, and 72 “Bangladesh Bank Heist” before listening to this one.
In May 2017 the world fell victim to a major ransomware attack known as WannaCry. One of the victims was UK’s national health service. Security researchers scrambled to try to figure out how to stop it and who was behind it.
Thank you to John Hultquist from FireEye and thank you to Matt Suiche founder of Comae.
Sponsors
Support for this episode comes from LastPass. LastPass is a great password manager but it can do so much more. It can setup 2FA for your company, or use it to monitor what your users are doing in the network. Visit LastPass.com/Darknet to start your 14 day free trial.
This episode was sponsored by Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and when signing up with a new account use code darknet2020 to get a $20 credit on your next project.
A bank robbery with the objective to steal 1 billion dollars. This is the story of the largest bank robbery in history. And it was all done over a computer.
Our guest this episode was Geoff White. Learn more about him at geoffwhite.tech.
Check out Geoff’s new book Crime Dot Com. Affiliate link: https://www.amazon.com/gp/product/1789142857/ref=as_li_tl?ie=UTF8&camp=1789&creative=9325&creativeASIN=1789142857&linkCode=as2&tag=darknet04-20&linkId=bb5a6aa7ba980183e0ce7cee1939ea05
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
In this episode, we’re going into the depths of North Korea to conduct one of the greatest hacks of all time. To find a way to inject information into a country run by totalitarian regime.
A big thanks to Yeonmi Park for sharing her story with us. Also thanks to Alex Gladstein for telling us the inside story.
You can find more about Flash Drive For Freedom at flashdrivesforfreedom.org.
Yeonmi’s book "In Order to Live": https://www.amazon.com/gp/product/014310974X/ref=as_li_tl?ie=UTF8&camp=1789&creative=9325&creativeASIN=014310974X&linkCode=as2&tag=darknet04-20&linkId=88ebdc087c6ce041105c479b1bb6c3d2
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Ghost Exodus is a hacker. He conducted various illegal activities online. Some of which he documents on YouTube. He’s also a great musician. He got into some trouble from his hacking. This is his story.
A big thanks to Ghost Exodus for sharing his story with us. Also thanks to Wesley McGrew for telling us the inside story.
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
This episode was sponsored by Detectify. What vulnerabilities will their crowdsource-powered web vulnerability scanner detect in your web applications? Find out with a 14-day free trial. Go to https://detectify.com/Darknet
Sources
We all know that computers and networks are vulnerable to hacking and malicious actors, but what about us, the humans who interface with these devices? Con games, scams, and strategic deception are far older than computers, and in the modern era, these techniques can make humans the weakest link in even the most secure system. This episode, security consultant and master social engineer, Christopher Hadnagy, joins us to share his stories and wisdom. He describes what it was like to be a social engineer before the world knew what social engineering was and tells some of his amazing stories from his long career in penetration testing.
A big thanks to Christopher Hadnagy from social-engineer.org for sharing his stories with us.
Check out his book Social Engineering: The Science of Human Hacking, affiliate link here.
Check out his podcast called The Social-Engineer podcast.
Sponsors
This episode was sponsored by Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this episode comes from LastPass. LastPass is a great password manager but it can do so much more. It can setup 2FA for your company, or use it to monitor what your users are doing in the network. Visit LastPass.com/Darknet to start your 14 day free trial.
Sources
Book Recommendations with affiliate links:
A mysterious mechanical failure one fateful night in a Saudi Arabian chemical plant leads a cast of operational technology researchers down a strange path towards an uncommon, but grave, threat. In this episode, we hear how these researchers discovered this threat and tried to identify who was responsible for the malware behind it. We also consider how this kind of attack may pose a threat to human life wherever there are manufacturing or public infrastructure facilities around the world.
A big thanks to Julian Gutmanis, Naser Aldossary, Marina Krotofil, and Robert M. Lee for sharing their stories with us.
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
This episode was sponsored by Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and when signing up with a new account use code darknet2020 to get a $20 credit on your next project.
Sources
John Strand is a penetration tester. He’s paid to break into computer networks and buildings to test their security. In this episode we listen to stories he has from doing this type of work.
Thanks to John Strand for coming on the show and telling your story.
Sponsors
Support for this episode comes from LastPass. LastPass is a great password manager but it can do so much more. It can setup 2FA for your company, or use it to monitor what your users are doing in the network. Visit LastPass.com/Darknet to start your 14 day free trial.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Sources
Freakyclown is a physical penetration tester. His job is to break into buildings to test the security of the building. In this episode we hear stories of some of these missions he’s been on.
Thanks to Freakyclown for coming on the show and telling your story.
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
This episode was sponsored by Molekule, a new air purifier that completely destroys air pollutants to help you breath easier. https://molekule.com.
PSYOP, or “Psychological Operations”, is something the US military has been doing to foreign audiences for decades. But what exactly is it? And what’s the difference between white, gray, and black PSYOP missions? We talk to PSYOP specialists to learn more.
Thanks to Jon Nichols for telling us about this fascinating world.
Sponsors
Support for this episode comes from LastPass. LastPass is a great password manager but it can do so much more. It can setup 2FA for your company, or use it to monitor what your users are doing in the network. Visit LastPass.com/Darknet to start your 14 day free trial.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Sources
Videos
Vodafone Greece is the largest telecom provider in Greece. But in 2004 a scandal within the company would pin them to be top of the news cycle in Greece for weeks. Hackers got in the network. And what they were after took everyone by surprise.
Sponsors
Support for this episode comes from Okta. Learn more about how you can improve your security posture with the leader in identity-driven security at okta.com/darknet.
This episode is supported by PlexTrac. PlexTrac is the purple teaming platform and is designed to streamline reporting, tracking and attestation so you can focus on getting the real cybersecurity work done. Whether you're creating pen test reports on the red team, or tracking and remediating on the blue team, PlexTrac can help.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
The hacker named w0rmer was active within AnonOps. These are Anonymous Operations which often organize and wage attacks on websites or people often with the purpose of social justice. Eventually w0rmer joined in on some of these hacking escapades which resulted in an incredible story that he will one day tell his kids.
Thanks to w0rmer for telling us your story.
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this episode comes from LastPass. LastPass is a great password manager but it can do so much more. It can setup 2FA for your company, or use it to monitor what your users are doing in the network. Visit LastPass.com/Darknet to start your 14 day free trial.
SourcesArchived Tweets
Feb 7, 2012 Twitter user @Anonw0rmer posts “@MissAnonFatale I managed to pwn1 a site , get my papers , find my required primary IDS , yeah baby, i deservers em :)”
Feb 8, 2012 1:17 AM, Twitter user @Anonw0rmer posted, “ROFL! WaS that us? https://www.wvgazettemail.com/news/legal_affairs/hackers-group-posts-police-chiefs-information-online/article_77f79fd5-f76f-5825-ae19-43a398361fdf.html o yeah oops #OpPigRoast #CabinCr3w”
Feb 9, 2012 12:35 AM, Twitter user @Anonw0rmer posted, “DB Leak http://dps.alabama.gov https://pastehtml.com/view/bnik8yo1q.html”. The bottom of this post originally showed this NSFW image.
Feb 9, 2012 at 8:42 PM, Twitter user @Anonw0rmer posted, “Mobile Alabama Police Criminal Record Database Logins Failing To Protect And Serve I Via @ItsKahuna I http://pastehtml.com/view/bnmjxxgfp.html #OpPiggyBank.”
Feb 9, 2012 at 8:39 PM, Twitter user @CabinCr3w posted, “Texas Dept. of safety Hacked By @AnonWOrmer for #OpPiggyBank http://bit.ly/x1KH5Y #CabinCr3w #Anonymous” Bottom of pastebin also shows a woman holding a sign saying “We Are ALL Anonymous We NEVER Forgive. We NEVER Forget. <3 @Anonw0rmer”
Feb 10, 2012 at 9:07 PM, Twitter user @Anonw0rmer posted, “My baby SETS standards ! wAt U got? https://i.imgur.com/FbH2K.jpg https://i.imgur.com/zsPvm.jpg https://i.imgur.com/S2S2C.jpg https://i.imgur.com/TVqdN.jpg #CabinCr3w”.
Links
Cam’s story is both a cautionary tale and inspirational at the same time. He’s been both an attacker and defender. And not the legal kind of attacker. He has caused half a million dollars in damages with his attacks. Attacks that arose from a feeling of seeing injustices in the world. Listen to his story.
Sponsors
This episode was sponsored by Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and when signing up with a new account use code darknet2020 to get a $20 credit on your next project.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Sources
Samy Kamkar is a hacker. And while he’s done a lot of stuff, he’s best known for creating the Samy Worm. Which spread its way through a popular social media site and had crazy results.
Thanks to our guest Samy Kamkar for telling his story. Learn more about him by visiting https://samy.pl/.
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this episode comes from LastPass. LastPass is a great password manager but it can do so much more. It can setup 2FA for your company, or use it to monitor what your users are doing in the network. Visit LastPass.com/Darknet to start your 14 day free trial.
Sources
This is a story about the hacker named “dawgyg” and how he made over $100,000 in a single day, from hacking.
Thanks to our guest dawgyg for telling his story.
Sponsors
This episode is sponsored by SentinelOne - to learn more about their endpoint security solutions and get a 30-day free trial, visit sentinelone.com/darknetdiaries
This episode was sponsored by Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and when signing up with a new account use code darknet2020 to get a $20 credit on your next project.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Sources
In this episode we hear from Gary and Justin. Two seasoned penetration testers who tell us a story about the time when they tried to break into a courthouse but it went all wrong.
Sponsors
This episode was sponsored by Detectify. Try their web vulnerability scanner free. Go to https://detectify.com/?utm_source=podcast&utm_medium=referral&utm_campaign=DARKNET
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Sources
OxyMonster sold drugs on the darknet at Dream Market. Something happened though, and it all came crashing down.
Sponsors
This episode was sponsored by Detectify. Try their web vulnerability scanner free. Go to https://detectify.com/?utm_source=podcast&utm_medium=referral&utm_campaign=DARKNET
This episode was sponsored by Molekule, a new air purifier that completely destroys air pollutants to help you breath easier. https://molekule.com to use check out code “DARKNET10” to get a discount.
See complete list of sources at https://darknetdiaries.com/episode/58.
Hear what goes on internally when Microsoft discovers a major vulnerability within Windows.
Guest
Thanks to John Lambert for sharing this story with us.
Sponsors
Support for this episode comes from ProCircular. Use the team at ProCircular to conduct security assessments, penetration testing, SIEM monitoring, help with patches, or do incident response. Visit www.procircular.com/ to learn more.
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Sources
Attribution
Darknet Diaries is created by Jack Rhysider.
Episode artwork by odibagas.
Theme music created by Breakmaster Cylinder. Theme song available for listen and download at bandcamp. Or listen to it on Spotify.
This is the story of Jordan Harbinger. A bit of a misfit teenager, who was always on the edge of trouble. In this story we hear what happened that lead to a visit from the FBI.
Guest
Thanks to Jordan Harbinger for sharing his story with us. You can find hist podcast by searching for The Jordan Harbinger Show wherever you listen to podcasts.
Sponsors
This episode was sponsored by Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
More information at https://darknetdiaries.com/episode/56.
A holiday special episode. A private pen tester takes on a job that involves him with another eccentric pen tester, a mischievious smile, and his quest to gain access to the network.
Guest
Thanks to TinkerSec for telling us the story.
Sources
Attribution
Darknet Diaries is created by Jack Rhysider.
Artwork this episode by habblesthecat.
More information at DarknetDiaries.com.
The story of NotPetya, seems to be the first time, we see what a cyber war looks like. In the summer of 2017 Ukraine suffered a serious and catastrophic cyber attack on their whole country. Hear how it went down, what got hit, and who was responsible.
Guest
Thanks to Andy Greenberg for his research and sharing this story. I urge you to get his book Sandworm because it’s a great story.
Sponsors
This episode was sponsored by Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and when signing up with a new account use code darknet2019 to get a $20 credit on your next project.
Support for this episode comes from Honeybook. HoneyBook is an online business management tool that organizes your client communications, bookings, contracts, and invoices – all in one place. Visit honeybook.com/darknet to get 50% off your subscription.
This episode was sponsored by CMD. Securing Linux systems is hard, let CMD help you with that. Visit cmd.com/dark to get a free demo.
For more show notes visit darknetdiaries.com/episode/54.
The NSA has some pretty advanced, super secret, hacking tools. What if these secret hacking tools were to end up in the wrong person’s hands? Well, that happened.
Guest
Thanks to Jake Williams from Rendition Security for telling us the story.
Sponsors
This episode was sponsored by Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
Credit card skimming is growing in popularity. Gas pumps all over are seeing skimmers attached to them. It’s growing in popularity because it’s really effective. Hackers have noticed how effective it is and have began skimming credit cards from websites.
Guest
Thanks to Yonathan Klijnsma from RiskIQ.
Sponsors
This episode was sponsored by Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and when signing up with a new account use code darknet2019 to get a $20 credit on your next project.
Support for this episode comes from Honeybook. HoneyBook is an online business management tool that organizes your client communications, bookings, contracts, and invoices – all in one place. Visit honeybook.com/darknet to get 50% off your subscription.
This episode was sponsored by CMD. Securing Linux systems is hard, let CMD help you with that. Visit https://cmd.com/dark to get a free demo.
Visit darknetdiaries.com for full show notes and transcripts.
Kashmir is a region right in between India, Pakistan, and China. For the last 70 years Pakistan and India have fought over this region of the world, both wanting to take control of it. Tensions sometimes heat up which can result in people being killed. When tensions get high in the real world, some people take to the internet and hack their rivals as a form of protest. In this episode we’ll explore some of the hacking that goes on between India and Pakistan.
Sponsors
Support for this episode comes from Check Point. Check Point makes firewalls and security appliances you can use to combat the latest generation of cyber attacks. Upgrade your cybersecurity at CheckPoint.com
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
For more show notes and links visit https://darknetdiaries.com/episode/51.
Operation Inherent Resolve was started in 2016 which aimed to combat ISIS. It was a combined joint task force lead by the US military. Operation Inherent Resolve sent troops, ships, and air strikes to Iraq and Syria to fire weapons upon ISIS military. It’s widely known that US military engaged with ISIS in this way. But what you may not have heard, is the story of how the US military also combated ISIS over the Internet. This is the story of how the US hacked ISIS.
Sponsors
This episode was sponsored by Linode. Linode supplies you with virtual servers. Visit linode.com/darknet and when signing up with a new account use code darknet2019 to get a $20 credit on your next project.
Support for this episode comes from Honeybook. HoneyBook is an online business management tool that organizes your client communications, bookings, contracts, and invoices – all in one place. Visit [honeybook.com/darknet] to get 50% off your subscription.
Support for this episode comes from Check Point. Check Point makes firewalls and security appliances you can use to combat the latest generation of cyber attacks. Upgrade your cybersecurity at CheckPoint.com
In this episode we meet Elliot Alderson (@fs0c131y) from Twitter. Who is this strange masked person? What adventures have they gotten themselves into? Many stories will be told. The mask will be lifted.
Sponsors
This episode was sponsored by Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Go to https://nordvpn.com/darknet to get 70% off a 3 year plan and use code darknet for an extra month for free!
This is the story about when a nation state hacks into a company within another nation.
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. And use promo code DARKNET25 to get 25% off.
This episode was sponsored by Nord VPN. Visit https://nordvpn.com/darknet and use promo code “DARKNET” to get 75% off when signing up for 3 years.
This is the story about an ex-NSA agent who went to work for a secret hacking group in the UAE.
Sponsors
This episode was sponsored by Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn’t be. Check them out at https://canary.tools.
Support for this episode comes from Blinkist. They offer thousands of condensed non-fiction books, so you can get through books in about 15 minutes. Check out Blinkist.com/DARKNET to start your 7 day free trial and get 25% off when you sign up.
This is the story about the XBox hacking scene and how a group of guys pushed their luck a little too far.
This is part 2 of a 2 part series.
Sponsors
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet.
Learn more about stocks and investing from MyWallSt. Visit mywallst.com/darknet to learn more.
This is the story about the XBox hacking scene and how a group of guys pushed the hacking a little too far.
This is part 1 of a 2 part series.
Sponsors
This episode was sponsored by Nord VPN. Visit https://nordvpn.com/darknet and use promo code "DARKNET".
This episode was sponsored by Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn't be. Check them out at https://canary.tools.
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet. Use promot code "DARKNET25".
Ransomware is ugly. It infects your machine and locks all the the data and to unlock you have to pay a fee. In this episode we dive into some of the people behind it.
Sponsors
This episode was sponsored by CMD. Securing Linux systems is hard, let CMD help you with that. Visit https://cmd.com/dark to get a free demo.
This episode was sponsored by MyWallSt. Their app can help you find good looking stocks to invest in. Visit MyWallSt.com/dark to start your free 30 day trial.
For more show notes and links check out darknetdiaries.com.
This is the story about how I acquired a black badge from DEFCON (pictured above).
We also hear the story about who PPP is, and their CTF journey at DEFCON.
This episode was sponsored by Nord VPN. Visit https://nordvpn.com/darknet and use promo code “DARKNET”.
This episode was sponsored by Detectify. Try their web vulnerability scanner free. Go to https://detectify.com/?utm_source=podcast&utm_medium=referral&utm_campaign=DARKNET
Three stories in one episode. Listen in on one of Dave Kennedy's penetration tests he conducted where he got caught trying to gain entry into a datacenter. Listen to a network security engineer talk about the unexpected visitor found in his network and what he did about it. And listen to Dan Tentler talk about a wild and crazy engagement he did for a client.
Guests
A very special thanks to Dave Kennedy. Learn more about his company at trustedsec.com.
Thank you Clay for sharing your story. Check out the WOPR Summit.
Viss also brought an amazing story to share. Thank you too. Learn more about him at Phobos.io.
I first heard Clay's story on the Getting Into Infosec Podcast. Thanks Ayman for finding him and bring that story to my attention.
Sponsors
This episode was sponsored by CMD. Securing Linux systems is hard, let CMD help you with that. Visit https://cmd.com/dark to get a free demo.
This episode was sponsored by Thinkst Canary. Their canaries attract malicious actors in your network and then send you an alert if someone tries to access them. Great early warning system for knowing when someone is snooping around where they shouldn't be. Check them out at https://canary.tools.
For more show notes and links check out darknetdiaries.com.
Join JekHyde and Carl on a physical penetration test, a social engineering engagagement, a red team assessment. Their mission is to get into a building they shouldn't be allowed, then plant a rogue computer they can use to hack into the network from a safe place far away.
This episode was sponsored by Nord VPN. Visit https://nordvpn.com/darknet and use promo code "DARKNET".
This episode was sponsored by Hostinger. Go to https://hostinger.com/darknet and use code DARKNET to get 15% off a hosting plan and check out this week’s free feature.
For more information visit darknetdiaries.com.
Take a ride with a red teamer. A physical penetration tester as he tries to make his away into unauthorized areas, steal sensitive documents, hack into the computers, and escape with company property.
This episode was sponsored by CMD. Securing Linux systems is hard, let CMD help you with that. Visit https://cmd.com/dark to get a free demo.
This episode was sponsored by Hostinger. Go to https://hostinger.com/darknet and use code DARKNET to get 15% off a hosting plan and check out this week’s free feature.
For complete show notes and links go to darknetdiaries.com.
A talk at Defcon challenged people to find a way to destroy a hard drive. A young man was inspired by this challenge and was determined to find a way to destroy a hard drive. But this is not a typical young man, with a typical plan.
For pictures of Daniel and his projects visit darknetdiaries.com/episode/39.
This episode was sponsored by Nord VPN. Visit nordvpn.com/darknet and use promo code "DARKNET".
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet.
A journalist wrote articles critical of the Kazakhstan government. The government did not like this and attempted to silence her. But they may have done more than just silence her. Perhaps they tried to spy on her too. The EFF investigated this case and went down a very interesting rabbit hole.
Thanks to Cooper Q from EFF's new Threat Lab. Also big thanks to Eva from EFF, Andrew Blaich and Michael Flossman from Lookout.
For another story about the EFF listen to episode 12 "Crypto Wars".
This episode was sponsored by CMD. Securing Linux systems is hard, let CMD help you with that. Visit https://cmd.com/dark to get a free demo.
The Venetian casino in Las Vegas Nevada was the largest hotel in the world until 2015. The parent company is Las Vegas Sands (LVS) which owns 10 properties around the world. And the CEO and founder of LVS is Sheldon Adelson. One day the CEO said something which sparked quite a firestorm.
This episode was sponsored by Nucleus. Visit nucleussec.com to start your free trial.
This episode was sponsored by CMD. Securing Linux systems is hard, let CMD help you with that. Visit https://cmd.com/dark to get a free demo.
For more show notes visit DarknetDiaries.com.
A company hires a penetration tester to pose as a new hire, Jeremy from Marketing, to see how much he can hack into in his first week on the job. It doesn't go as planned.
Thanks to @TinkerSec for telling us this story.
This episode was sponsored by Nord VPN. Visit https://nordvpn.com/darknet and use promo code "DARKNET".
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet.
For more show notes visit https://darknetdiaries.com/episode/36.
ATM hacking. Hollywood has been fantasizing about this since the 1980's. But is this a thing now? A security researcher named Barnaby Jack investigated ATMs and found them to be vulnerable. Once he published his data the ATM hacking scene rose in popularity and is is a very serious business today.
One of the first big ATM robberies was done with the malware called Carbanak. Jornt v.d. Wiel joins us to discuss what this malware is.
This episode was sponsored by Nucleus. Visit nucleussec.com to start your free trial.
This episode was sponsored by IT Pro TV. Get 65 hours of free training by visiting ITPro.tv/darknet.
For more show notes and links visit darknetdiaries.com.
Nude selfies. This episode is all about nude selfies. What happens if you take one and give it to a vengeful boyfriend. What happens when a hacker knows you have them and wants to steal them from your phone. What happens is not good.
This episode was sponsored by Nord VPN. Visit nordvpn.com/darknet and use promo code "DARKNET".
This episode was sponsored by Molekule, a new air purifier that completely destroys air pollutants to help you breath easier. Visit molekule.com to use check out code "DARKNET" to get a discount.
For references, sources, and links check out the show notes at darknetdiaries.com/episode/34/.
In 2009 a hacker broke into a website with millions of users and downloaded the entire user database. What that hacker did with the data has changed the way we view account security even today.
This episode was sponsored by CuriosityStream. A streaming service showing non-fiction and documtnaries. Visit https://curiositystream.com/darknet and use promo code "darknet".
This episode was sponsored by CMD. Securing Linux systems is hard, let CMD help you with that. Visit https://cmd.com/dark to get a free demo.
To see more show notes visit darknetdiaries.com/episode/33.
A carding kingpin was tracked by the Secret Service. How did he steal the cards? Where was he stealing them from? How much was he making doing this? And where did he go wrong? Find out all this and more as we listen to how the Secret Service investigated the case.
This episode was sponsored by Eero. A solution to blanket your home in WiFi. Visit https://eero.com/darknet and use promo code "darknet".
This episode was sponsored by Nord VPN. Visit https://nordvpn.com/darknet and use promo code "darknet".
Cover image this episode created by 𝕄årç ∆⃝ 𝕄ølïñårō.
Go to Darknet Diaries for additional show notes.
In late November 2018, a hacker found over 50,000 printers were exposed to the Internet in ways they shouldn't have been. He wanted to raise awareness of this problem, and got himself into a whole heap of trouble.
For show notes and links visit DarknetDiaries.com.
This episode was sponsored by CuriosityStream. A documentary streaming service. Visit curiositystream.com/darknet and use promo code "darknet".
This episode is also sponsored by Cover. Visit cover.com/darknet to get insured today.
In 2012, Saudi Aramco was hit with the most destructive virus ever. Thousands and thousands of computers were destroyed. Herculean efforts were made to restore them to operational status again. But who would do such an attack?
Very special thanks goes to Chris Kubecka for sharing her story.
She is author of the book Down the Rabbit Hole An OSINT Journey, and Hack The World With OSINT (due out soon).
This episode was sponsored by Eero. A solution to blanket your home in WiFi. Visit https://eero.com/darknet and use promo code "darknet".
This episode is also sponsored by Cover. Visit cover.com/darknet to get insured today.
Stuxnet was the most sophisticated virus ever discovered. It's target was a nuclear enrichment facility in Iran. This virus was successfully able to destroy numerous centrifuges. Hear who did it and why.
Special thanks to Kim Zetter for joining us this episode. You can find more about Stuxnet from her book Count Down to Zero Day.
Israel has their own version of the NSA called Unit 8200. I was curious what this unit does and tried to take a peek inside. Hear what I found by listening along to this episode.
This episode was sponsored by Nord VPN. Visit https://nordvpn.com/darknet and use promo code “darknet”.
This episode is also sponsored by Mack Weldon. Visit mackweldon.com to shop for premium men's casual wear and get a 20% off discount with your first order by using promo code “diaries”.
Something is wrong with the Apple Podcasts top charts. As a podcaster, this personally annoyed and intrigued me. I investigate how this is happening and who is behind it.
For show notes visit https://darknetdiaries.com/episode/27.
This episode was sponsored by Nord VPN. Visit https://nordvpn.com/darknet and use promo code 'darknet'.
This episode is sponsored by LPSS Digital Marketing, your source for honest, transparent marketing services for businesses of all sizes. Visit LPSS at https://www.lpss.co/ for details.
The IRS processes $3 trillion dollars a year. A lot of criminals want to get a piece of that. In 2015 the IRS had a large data breach. Hundreds of thousands of tax records were leaked. What happened and who was behind this? Listen to this episode to find out.
For show notes visit https://darknetdiaries.com
Alberto Hill was sent to prison for a long time for hacking. For a crime he said he did not commit. Listen to his story and you be the judge on whether he's guilty or not.
Darknet markets are online black markets. They are highly illegal, and dangerous to run. Hear exactly how dangerous it was for Alphabay and Hansa dark markets.
When banks started coming online, they almost immediately started being targeted by hackers. Vladimir Levin was one of the first ever known hacker to try to rob a bank. He succeeded a little, and failed a lot. Vladimir would go down in the history books as one of the most notorious hackers of all time because of his attempted online bank robberies.
Three stories in one! In this episode we hear about a penetration test from Mubix that he'll never forget, a incident response from Robert M. Lee which completely stunned him, and a social engineering mission from Snow.
Podcast recommendation: Moonshot.
Ira Winkler's specialty is assembling elite teams of special forces and intelligence officers to go after companies. Ira shares a story about a time he and his team broke into a global 5 company. A company so large that theft of intellictual property could result in billions of dollars of damage.
Ira's consulting company: Secure Mentum.
His books: Spies Among Us, Advanced Persistent Security, Through the Eyes of the Enemy.
Chances are, if you were downloading shady programs in the early 2000's, you were infected with malware he wrote called SubSeven. Hacking changed mobman's life. Hear how it happened by listening to this episode.
Image for this episode created by dr4w1ngluc4s. Check out his Instagram to see some amazing artwork!
Check out the podcasts Van Sounds and True Crime Island
In 2009, around Christmas time, something terrible was lurking in the network at Google. Google is the most popular website on the Internet. It’s so popular many people just think Google is the Internet. Google hires many of the most talented minds and has been online since the 90s. Hacking into Google is no easy task. There’s a team of security engineers who test and check all the configurations on the site before they go live. And Google has teams of security analysts and technicians watching the network 24/7 for attacks, intrusions, and suspicious activity. Security plays a very vital role at Google, and everything has to have the best protections. But this attack slipped past all that. Hackers had found their way into the network. They compromised numerous systems, burrowed their way into Google’s servers, and were trying to get to data they shouldn’t be allowed to have. Google detected this activity. And realized pretty quickly they were dealing with an attack more sophisticated than anything they’ve ever seen.
Podcast recommendation: Twenty Thousand Hertz
A man addicted to gambling finds a bug in a video poker machine that lets him win excessive amounts of money.
A 14-year-old kid who finds himself bored in class decides to hack someone's twitter account and ends up with more than he bargained for.
In 2007, a hacker named Eijah got fed up with the way DRM prevented him from being able to play the content he paid for. He decided to fight back against the AACS and find a way to circumvent the DRM. By the time Eijah was done, his life wasn't the same.
A major retailer was hacked. Their point of sales machines were riddled with malware. Listen to hear how digital forensics and incident responders handled the situation. What malware was found? Where was it found? How was it stopped? And most importantly, how much data was leaked?
In 2013 a hospital was accused of conducting a medical kidnapping against a young girl name Justina. This enraged many people across the country, including members of anonymous. A DDOS attack was waged against the hospital.
In 2012 the Carna Bot was built and unleashed on the world. But it didn't have any intentions on doing anything malicious. It was built just to help us all understand the Internet better. This botnet used the oldest security vulnerable in the book. And the data that came out of it was amazing.
In the 1990's the Internet started to take shape. But the US goverment had strict laws regulating what type of cryptography is allowed to be used online. A few brave people stood up to the government in the name of civil rights and won the right to use strong encryption. Listen to their battle and what they had to do through to accomplish this.
What happens when an innovative tech company, that's trying to develop the next big thing, detects a hacker in their network? We hear the story from a digital forensics investigator which has a surprising result.
In today's world of intelligence gathering, governments hack other governments. This episode takes you on a ride with a nation state actor to see exactly how it's done.
Mt. Gox was the largest bitcoin exchange in the world. It suddenly went offline. What happened?
Manfred found a way to turn his passion for video games and reverse engineering into a full time business. He exploited video games and sold virtual goods and currency for real money. This was his full time job. Listen to this episode to hear exactly how he did this.
Manfred has had the most epic story of all online video game stories. For the last 20 years, he's been hacking online games.
Jayson E. Street tells us a story about the time he broke into a bank in Beirut Lebanon.
Security researcher Kyle Lovett bought a new Asus router in 2013. He found it was riddled with security vulnerabilties. He set out on a mission to resolve these vulnerabilities not only for his own router, but for thousands of others who were also vulnerable.
Mobile provider TalkTalk suffered a major breach in 2015. The CEO tried her best to keep angry customers calm and carry on. The UK government and Metropolitan Police investigate the breach. We get a rare glimpse of how the CEO handles the crisis.
The 2011 DigiNotar breach changed the way browsers do security. In this episode, we learn what role a CA plays, how browsers work with CAs, and what happens when a CA is breached.
VTech makes toy tablets, laptops, and watches for kids. In 2015, they were breached. The hacker downloaded gigs of children's data. Discover what the hacker did once he took the data.
Farhan Arshad and Noor Aziz Uddin were captured 2 years after being placed on the FBI's Cyber's Most Wanted list for PBX hacking. In this episode, we explain PBX hacking and how hackers are racking up billions of dollars in phone bills. We also learn how the two men were captured.